Compliance › Compliance
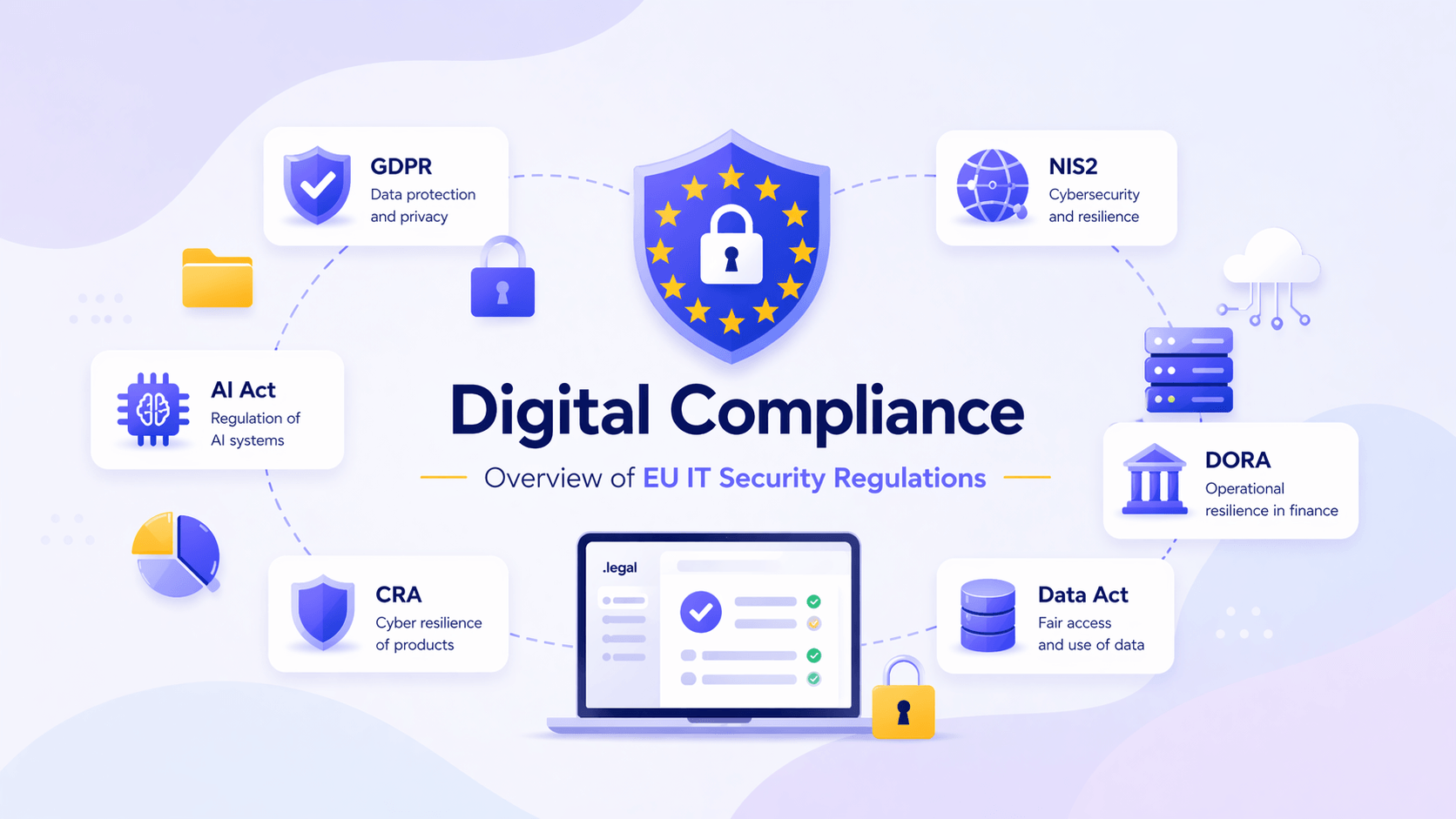
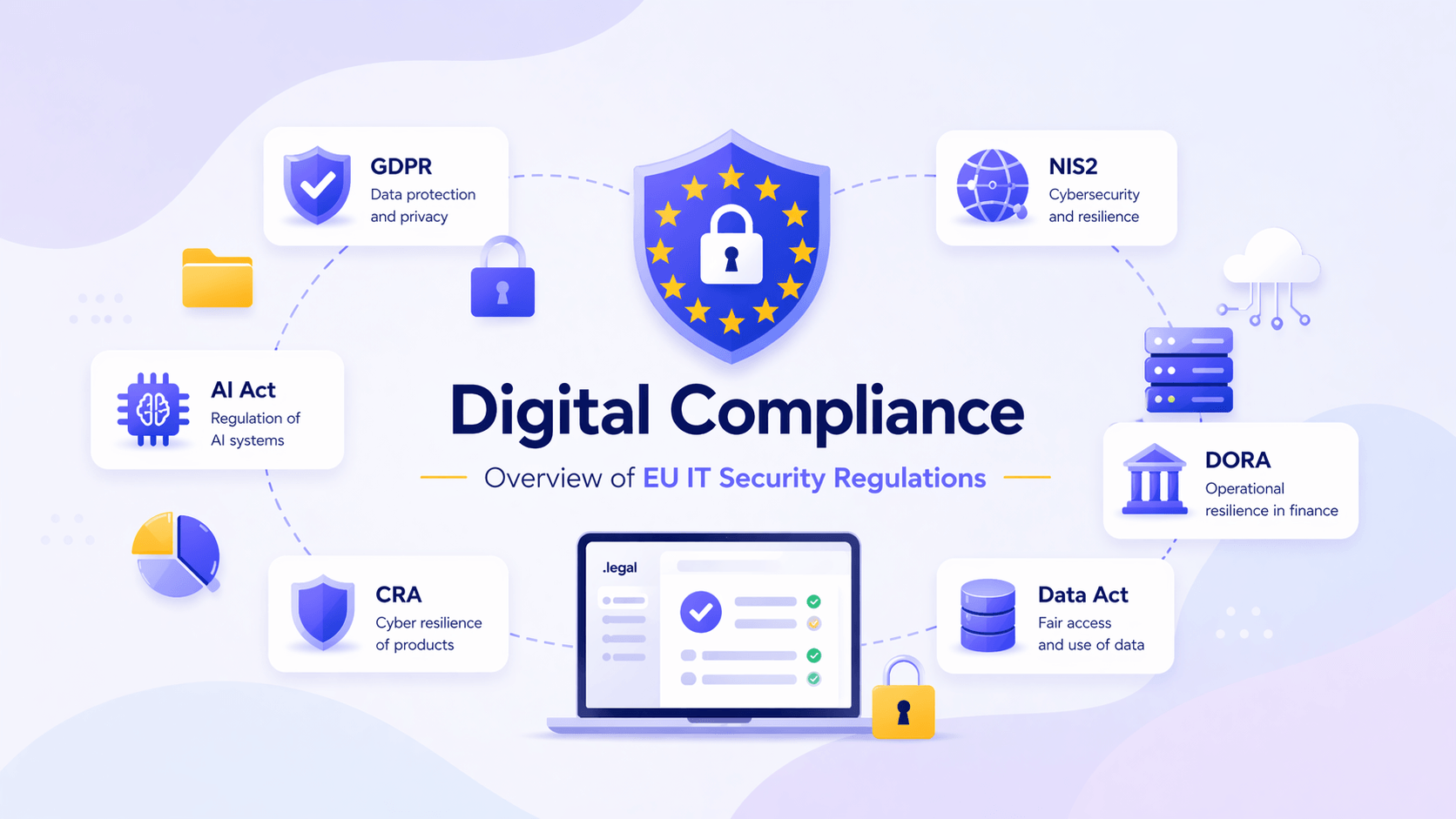
Digital Compliance

A security breach is an incident that compromises your organisation, whether it's an outsider slipping through the front door or an employee accidentally sending an email to the wrong recipient.
There are several perspectives on what constitutes a security breach.
In the context of IT security, a security breach is any incident that compromises your organisation's network and systems, whether it takes a server offline briefly or leaks all customer data.
When a security breach involves personal data, it's called a personal data breach and you must comply with the GDPR. If the breach instead compromises the company's network and disrupts operations or brings a critical service down, it's a cybersecurity incident covered by the NIS2 Directive.
The same security breach can be both a personal data breach under GDPR and an incident covered by NIS2, meaning you need to handle the requirements from both regulatory frameworks simultaneously and document the entire process.
Security breaches are therefore not just a technical problem but also a compliance challenge, because your organisation is subject to different regulations that must be followed when a breach occurs.
A personal data breach is a security incident under GDPR. It occurs when you lose control over the confidentiality, integrity, or availability of personal data, which can happen when personal data is lost, altered, destroyed, or shared with unauthorised parties.
.png?width=1536&height=1024&name=securitybreach-gdpr%20(1).png)
In practice, a personal data breach can range from a hacking attack or ransomware (where data is locked and a ransom demanded) to an employee sending information to the wrong recipient or losing a laptop on a train. A personal data breach can also occur internally if an employee intentionally or inadvertently shares data that shouldn't have been shared.
When a personal data breach occurs, you must notify the supervisory authority as soon as possible and no later than 72 hours after identifying the breach. If the breach is assessed as having no consequences for the data subject, notification isn't required, but in practice you'll often need to file one.
All identified personal data breaches must be documented in a log, regardless of whether they are reported to the supervisory authority. Your documentation should include:
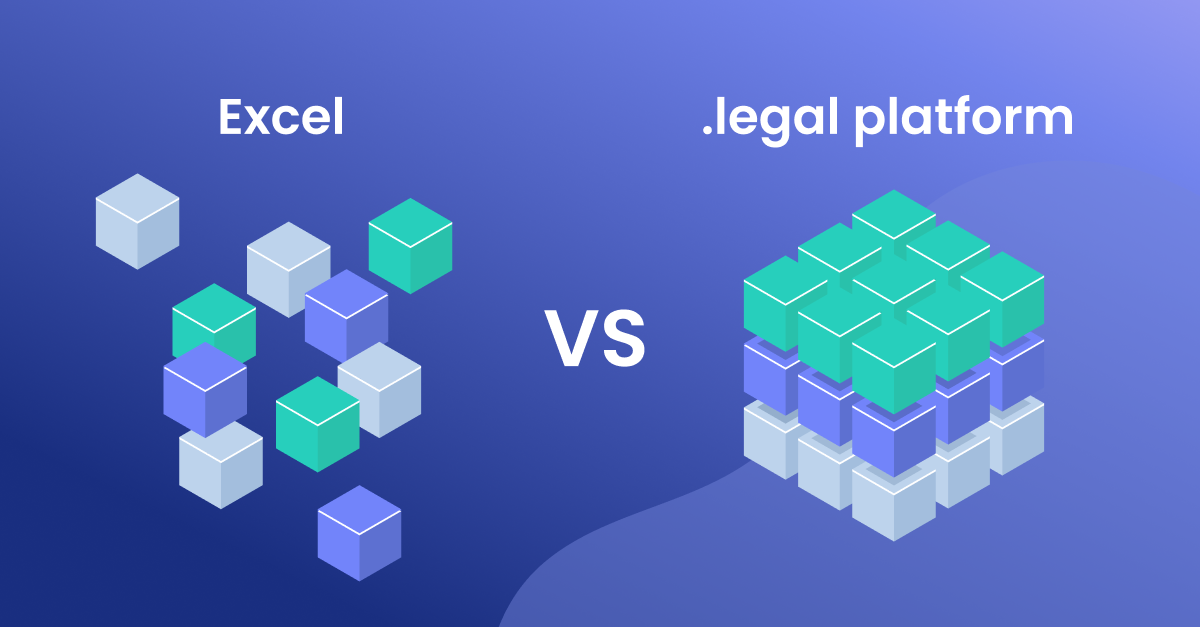
You can record this in a spreadsheet, GDPR compliance system, or similar tool.
You must also notify the affected individuals of a personal data breach if it's assessed that they will be negatively affected. This notification must be made as soon as possible so those affected can protect themselves against the consequences of the breach.
Under the NIS2 Directive, security breaches are viewed as incidents affecting network or information systems that disrupt or threaten to disrupt the operation of those systems.
An incident is considered significant if it has caused or is capable of causing severe operational disruptions to services or financial losses for the affected entity. It's also a significant incident if it has affected or is capable of affecting other persons or organisations by causing considerable damage.
.png?width=1536&height=1024&name=securitybreach-nis2%20(1).png)
Significant incidents must be reported to the national CSIRT (Computer Security Incident Response Team). In Denmark, this is the Centre for Cyber Security.
An early warning must be submitted within 24 hours of becoming aware of the significant incident. The warning should indicate whether the incident is suspected to be a deliberate act and whether it could have cross-border impact.
Within 72 hours of the significant incident, an updated notification must be submitted to the CSIRT, providing an initial assessment of the severity and impact and describing the indicators of the incident.
Within 1 month of the previous notification, a detailed report of the incident must be submitted, containing:
| Deadline | GDPR | NIS2 |
|---|---|---|
| Within 24 hours | No specific requirement | Early warning to CSIRT |
| Within 72 hours | Notification to supervisory authority | Updated notification to CSIRT |
| As soon as possible | Notification of data subjects | – |
| Within 1 month | – | Detailed incident report |
| Documentation | All breaches logged, regardless of notification | Documented procedures for risk management and incident handling |
A near-miss incident is an event that could have endangered the availability, authenticity, integrity, or confidentiality of stored, transmitted, or processed data, or of the services offered by or accessible via network and information systems, but was successfully prevented from materialising or did not materialise.
Essential and important entities may voluntarily submit notifications about near-miss incidents to the national CSIRT. This isn't a requirement but can be beneficial, as it provides an opportunity to consult with the national CSIRT to prevent similar incidents in the future.
This option also applies to organisations that are otherwise not covered by NIS2.
NIS2 also places a specific requirement on covered organisations to have documented procedures for both risk management and incident handling, so that incidents can be identified and managed.
This also means that measures must be implemented to prevent security breaches in network and information systems or to reduce their harmful effects.
According to the IBM "Cost of a Data Breach 2024" report, organisations identified just 42% of security incidents on their own, while external partners (e.g. authorities, ethical hackers) identified 34% on their behalf. The remaining 24% of security incidents were brought to organisations' attention by the attackers themselves.
When a company learns of a security breach from an external source, and particularly from the attackers themselves, the breach is typically more costly. Attackers only publicise their attacks after they've achieved their objective, which makes the breach more expensive to handle.
.png?width=1536&height=1024&name=securitybreach-report%20(1).png)
This is just one of several reasons why it's important to be able to identify security breaches internally.
Your IT department is primarily responsible for identifying security breaches by implementing appropriate technical and organisational measures, but what should everyone else in the organisation do?
First and foremost, your company should establish a procedure for how security breaches are handled, so you're not acting blindly when a breach occurs. Instead, you can take decisive action to contain the negative consequences.
The procedure should set guidelines for all employees who have a role in handling the breach. These employees should also be familiar with their role in advance.
It's important that employees responsible for compliance are involved in handling the breach from the start, so that all regulatory requirements are met immediately rather than as an afterthought. As outlined earlier, there are specific requirements in both GDPR and NIS2 that your organisation must comply with in the event of a security breach.
The compliance officer must ensure that the necessary documentation of the security breach and the company's response is prepared. This documentation is also used for reporting to the authorities and informing those affected by the breach (e.g. customers, users).
It's also important to involve management early, as the breach can have a significant impact on the company's operations, stakeholders, reputation, and finances. Quick decisions are critical in a crisis, so management should be kept informed and closely involved in the response.
A security breach can trigger both GDPR and NIS2 requirements, depending on whether personal data and/or business-critical systems are affected. It's crucial to be able to identify the breach and then document all actions before, during, and after the breach to comply with the applicable regulatory requirements.
To ensure your organisation is prepared to handle security breaches correctly, you should review your GDPR compliance checklist and make sure procedures are in place for both personal data breaches and cybersecurity incidents.
Want to see how .legal can help you document and manage security breaches across GDPR and NIS2? Book a demo and see the platform in action.
Under GDPR, a security breach (personal data breach) is a breach of security leading to accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to personal data. This covers a wide range of incidents from cyberattacks to accidental data exposure.
Organizations must assess the breach's severity, document all details, notify the relevant supervisory authority within 72 hours if the breach poses a risk to individuals' rights, and notify affected individuals without undue delay if the breach poses a high risk to their rights and freedoms.
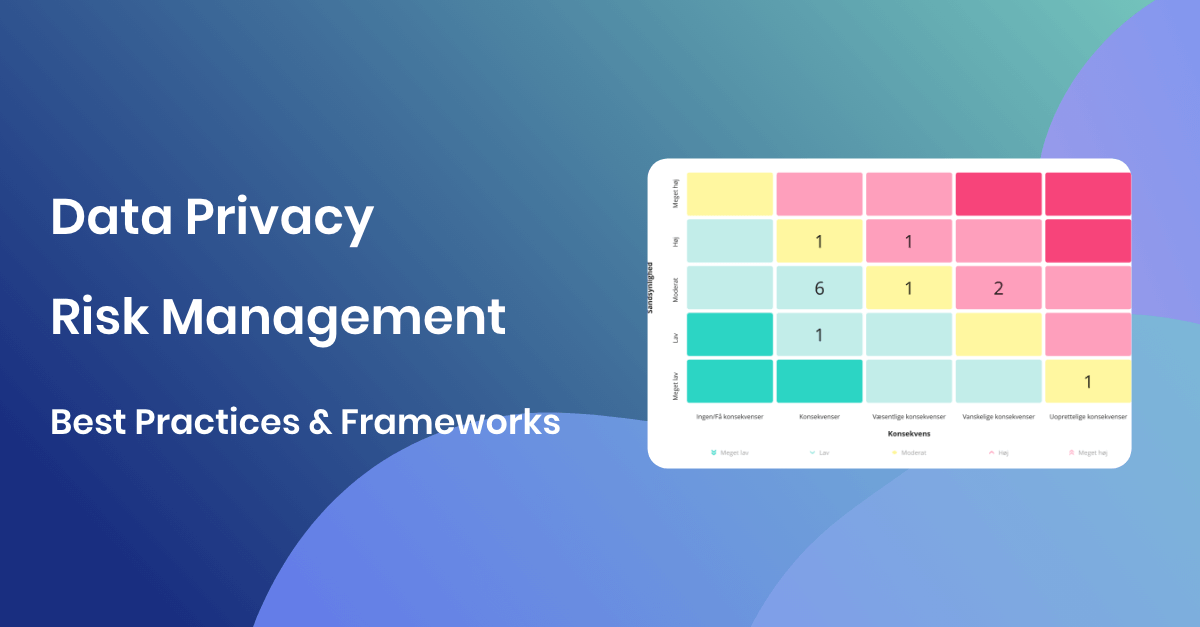
Assess severity by evaluating the type and sensitivity of data affected, number of individuals impacted, potential consequences for those individuals, whether data was encrypted, the likelihood of identification, and any special circumstances that could amplify the impact.
The notification must describe the nature of the breach, categories and approximate number of individuals affected, categories and approximate number of records concerned, name and contact details of the DPO, likely consequences of the breach, and measures taken or proposed to address it.
Common causes include phishing attacks, malware and ransomware, weak or compromised credentials, unpatched software vulnerabilities, human error such as misdirected emails, insider threats, improper data disposal, misconfigured systems, and third-party vendor compromises.
Prevention strategies include implementing strong access controls, regular security training, encryption of data at rest and in transit, regular vulnerability assessments, incident response planning, network monitoring, multi-factor authentication, patch management, and vendor security assessments.
GDPR fines for security breaches can reach up to 10 million euros or 2% of global annual turnover for inadequate security measures, and up to 20 million euros or 4% of global turnover for violations of data processing principles. Actual fines depend on the breach circumstances and organizational response.
Document the breach timeline, how it was discovered, data types and volume affected, individuals impacted, root cause analysis, immediate containment actions, long-term remediation measures, communication with authorities and affected individuals, and lessons learned. This documentation is required even for breaches not reported to authorities.
A breach response team coordinates the organization's response to security incidents. It typically includes IT security, legal, communications, management, and the DPO. The team manages containment, investigation, notification, remediation, and post-incident review to minimize damage and ensure regulatory compliance.
Compliance software provides incident management workflows, breach assessment tools, notification templates, deadline tracking, documentation management, communication logs, and reporting capabilities. It helps organizations respond quickly, meet regulatory deadlines, and maintain comprehensive records of breach handling.














.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.