Information Security Management › ISAE
Becoming Compliant: .legal's ISAE 3000 & ISAE 3402

There comes a moment in many organisations' lives when someone asks: "Should we just go ahead and get ISO 27001 certified?"
ISO 27001 certification is the formal confirmation that your organisation has a functioning ISMS (Information Security Management System) that meets the requirements of the international standard for information security. To achieve it, you need to define your scope, conduct a risk assessment, implement controls and policies, pass an external audit in two stages, and maintain the system on an ongoing basis. For most mid-sized organisations, the process takes 6 to 18 months and typically costs between £130,000 and £350,000 all in.

That may sound like a lot. But it is more achievable than most people expect when they first look at the requirements list.
This guide walks through the certification process step by step: what it requires, what it costs, and what most often causes delays.
ISO 27001 is the international standard for information security. More precisely, it defines what a functioning ISMS (Information Security Management System) requires.
An ISMS is not simply a collection of policies and documents. It is a management system that ensures information security is embedded in an organisation's day-to-day operations and decision-making. Confidentiality, integrity, and availability of information (the so-called CIA triad) sit at the centre of it.
ISO 27001 certification is the formal confirmation from an accredited certification body that your organisation meets the requirements of the standard. The certificate is valid for three years but requires ongoing surveillance audits, typically once a year.
The current version is ISO 27001:2022, which replaced the 2013 version. All certificates based on the 2013 version expired in October 2025, so the 2022 version is the one that applies today.
Read more about what ISO 27001 compliance involves.
The standard consists of two main parts: the mandatory clause requirements (clauses 4-10) and the controls in Annex A.
The clause requirements concern the management system itself:
Annex A contains 93 controls in the 2022 version, covering organisational, people, physical, and technological controls. The organisation must address all controls through a Statement of Applicability (SoA), which documents which controls are relevant and whether they have been implemented.
Optional does not mean irrelevant here. The Annex A controls are the output of the risk assessment. The standard requires you to document why any control has been excluded.
Check our ISO compliance checklist for a complete overview of the requirements, and read about information security risk management for deeper insight into the risk assessment process.
The path to certification typically follows six phases. The timeline varies depending on the organisation's size, complexity, and starting point.

The first step is to define the scope of the ISMS. Should it cover the entire organisation, or only specific departments, systems, or services?
The scope decision has significant implications for what needs to be documented and audited. A scope that is too narrow is risky, because critical systems may fall outside the ISMS. A scope that is too broad makes the project unnecessarily complex. Getting this right requires a deliberate and balanced assessment.
This is also where leadership commitment should be established and the project's resources confirmed.
Where does the organisation stand today? A thorough gap analysis maps what is already in place, what is missing, and what needs to improve. Many organisations discover at this stage that they are already doing a great deal correctly, they just have not documented it.
The gap analysis provides the foundation for the project plan and is essential for a realistic timeline estimate.
This is the most resource-intensive phase. Policies and procedures are drafted, risk assessments are conducted, Annex A controls are implemented, and staff are trained.
The structure and documentation requirements are clear, but the work is real. This is where a compliance management system can save a significant amount of time and reduce the risk of missing something along the way.
Before the external audit, the organisation must carry out an internal audit. The purpose is to verify that the ISMS is functioning as described and to identify any nonconformities before the formal review.
An internal audit is not a formality. It is a genuine quality check on whether the documentation matches actual practice.
The external audit takes place in two stages.
Stage 1 is a documentation review. The certification body examines whether the organisation's documentation is ready and covers the standard's requirements. It is an assessment of whether you are ready for the main audit. Typical findings here include missing or incomplete documents, for example an SoA that has not been updated or missing evidence of a management review.
Stage 2 is the main audit. The auditor verifies that what is documented is actually implemented in practice. Employees are interviewed, systems are inspected, and processes are reviewed. It is not an exam with right and wrong answers, but a systematic assessment of whether your ISMS is genuine and functional.

If Stage 2 is passed, the ISO 27001 certificate is issued. It is valid for three years but requires two surveillance audits (typically after year one and year two) and a recertification audit after three years.
Certification is not a project with an end date. It is an ongoing commitment. Organisations that treat it as a project and then ease off typically run into problems at subsequent surveillance audits.
Read more about what an ISMS involves in practice.
The honest answer: it varies. But a realistic timeline for a mid-sized organisation starting from scratch typically looks like this:
| Phase | Typical Duration |
|---|---|
| Preparation and gap analysis | 1-2 months |
| ISMS implementation | 3-9 months |
| Internal audit and remediation | 1-2 months |
| External audit and certification | 1-3 months |
| Total | 6-18 months |
Organisations with a mature security culture and existing documentation can move faster. Organisations with many systems, multiple departments, or complex supply chains typically sit at the upper end of the range.
An accelerated timeline of 4-6 months is possible, but requires dedicated resources and strong leadership commitment from day one.
Costs fall into three categories.

Internal resources are typically the largest cost and the hardest to estimate precisely. A realistic figure for a mid-sized organisation is 0.5 to 1 full-time equivalent dedicated to the project during the implementation phase.
External consultancy is used by many organisations for gap analysis, ISMS implementation, and preparation for the audit. Costs vary considerably, but budget for roughly £85,000 to £250,000 for an average implementation engagement.
Certification fees are the charges from the accredited certification body. For a mid-sized organisation, this typically falls in the range of £25,000 to £65,000 for the full certification process, including Stage 1, Stage 2, and the first surveillance audit.
A compliance management system that supports ISMS documentation, risk assessments, and auditing can meaningfully reduce internal resource costs, because the structure is in place from day one.
A question we hear often: Do we need ISO 27001 if we are already GDPR-compliant?
GDPR and ISO 27001 overlap, but they are not the same thing. GDPR is about protecting personal data. ISO 27001 is about information security in the broad sense, including systems, assets, and business processes that may not involve personal data at all. A strong ISO 27001 implementation supports GDPR compliance, but it is not a substitute for it.
For organisations subject to NIS2, ISO 27001 is even more relevant. The standard covers around 70-80% of NIS2's security requirements, and an ISO 27001 certification can make it significantly easier to demonstrate NIS2 compliance to national authorities.
The relationship is not either/or. It is more a question of what is mandatory (GDPR and potentially NIS2) and what makes strategic sense to work towards on top of that (ISO 27001).

Read our complete comparison of NIS2 and ISO 27001, where we go through the overlaps and gaps in detail.
Starting with controls rather than risks. The Annex A controls are responses to risks, not a checklist to be filled in for its own sake. Organisations that jump straight to the controls without a proper risk assessment end up with controls that do not match their actual risk profile. Auditors spot this.
Compliance theatre. The documents exist, but practice has not changed. Auditors are experienced at identifying this. An ISO 27001 audit is not a paper check. It is a verification of whether your security culture is genuine.
Insufficient leadership commitment. ISO 27001 requires active involvement from top management, not just a signature on a security policy. Certification programmes treated as IT projects without a leadership mandate consistently run into more difficulty.
Scope defined in haste. A poorly considered scope creates problems throughout the entire process. Invest time here at the start.
Underestimating the maintenance commitment. Many organisations focus on obtaining the certificate and underestimate what it takes to maintain it. An ISMS that is not actively kept up to date loses its effectiveness, and that becomes apparent at surveillance audits.
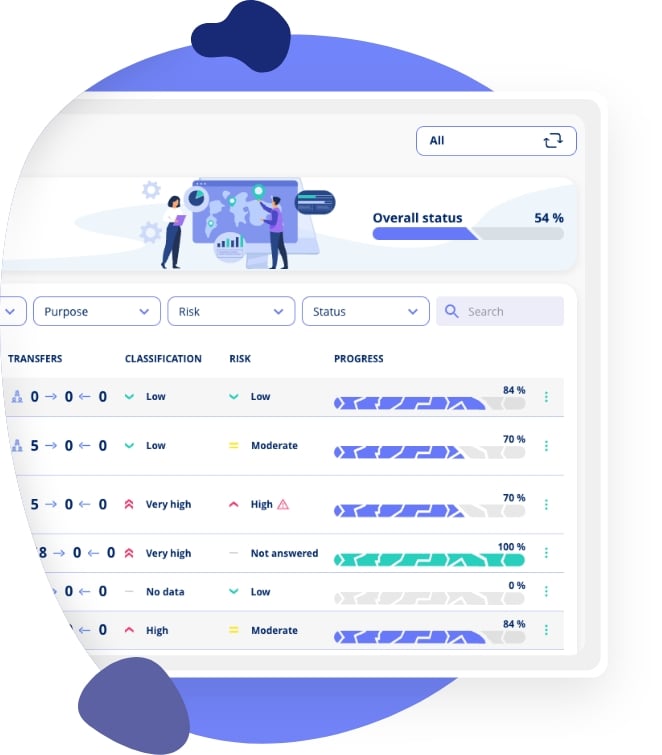
A compliance management system can make a real difference in a certification programme. Not because the documents write themselves, but because the structure and logic are in place from day one: risk assessments, controls, policies, Statement of Applicability, audit log, and ongoing follow-up, all in one place.

.legal's ISMS solution is built to support ISO 27001 requirements directly. See .legal's information security platform, or explore our frameworks module to see how the ISO 27001 framework is structured within the platform.
ISO 27001 certification is the formal confirmation from an accredited certification body that your organisation's ISMS (Information Security Management System) meets the requirements of the ISO/IEC 27001 standard. The certificate is valid for three years, with ongoing surveillance audits required each year.
ISO 27001:2022 updated Annex A from 114 controls in 14 domains to 93 controls in 4 themes, and added 11 new controls covering areas such as cloud security, threat intelligence, and secure coding. The clause structure remained largely unchanged. All certificates based on the 2013 version expired in October 2025.
Only accredited certification bodies can issue ISO 27001 certificates. Accreditation is granted by national accreditation bodies such as UKAS in the UK or DANAK in Denmark. Examples of active certification bodies include Bureau Veritas, DNV, and SGS.
For most mid-sized organisations, 6 to 18 months is a realistic estimate. The breakdown is typically: 1-2 months for preparation and gap analysis, 3-9 months for ISMS implementation, 1-2 months for internal audit and remediation, and 1-3 months for the external audit and certification.
Total costs depend on the organisation's size and starting point. Budget for certification body fees of roughly £25,000 to £65,000, potential consultancy fees of £85,000 to £250,000, and internal resources equivalent to 0.5 to 1 full-time equivalent during implementation. Most programmes land in the range of £130,000 to £350,000 overall.
A Statement of Applicability (SoA) is a key document in ISO 27001. For each of the standard's 93 Annex A controls, it documents whether the control is applicable to the organisation, whether it has been implemented, and the justification for any controls that have been excluded. It is typically one of the first documents a certification body reviews.
Stage 1 is a documentation review in which the auditor assesses whether the organisation's documentation is ready and covers the standard's requirements. Stage 2 is the main on-site audit, where the auditor verifies that what is documented is genuinely implemented in practice through interviews, system inspections, and process reviews.
No. ISO 27001 is a voluntary standard. No EU regulation specifically requires ISO 27001 certification, but for organisations subject to NIS2 or DORA, certification can make it significantly easier to demonstrate compliance with the security requirements of that legislation.
The certificate is valid for three years. Before it expires, a recertification audit must be completed. In between, two surveillance audits are required, typically after year one and year two. If the recertification audit is not carried out, the certificate lapses.
No. ISO 27001 is a voluntary standard; NIS2 is legislation with mandatory requirements for organisations in critical and important sectors. ISO 27001 does, however, cover around 70-80% of NIS2's security requirements, and certification can substantially strengthen the documentation of NIS2 compliance. The two are complementary, not interchangeable.
Want to dig deeper into ISMS, NIS2 and information security best practice? Explore our related articles on certification, compliance and risk management.
















.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.