
NIS2 › NIS2 Compliance
NIS2 Introduction

The NIS2 Directive requires organisations in critical and important sectors to conduct thorough risk assessments of their cybersecurity posture. This isn't just a compliance checkbox—it's about systematically understanding where your organisation is vulnerable and taking concrete steps to protect your critical services.
In this guide, we'll walk through the complete process of conducting a NIS2-compliant risk assessment, from identifying your critical services to creating actionable risk mitigation plans. We'll use practical examples throughout to show exactly how this works in practice.
A NIS2 risk assessment is a systematic process for identifying, analysing, and evaluating cybersecurity risks to your organisation's critical services and infrastructure. It's one of the core requirements in Article 21 of the NIS2 Directive.
The assessment helps you understand:
Unlike a general information security risk assessment, a NIS2 risk assessment specifically focuses on risks that could affect the continuity of your critical services and, by extension, the sectors and society you serve.

If your organisation is classified as an essential or important entity under NIS2, you must conduct regular risk assessments. This includes organisations in sectors such as:
The key criterion is whether your organisation provides services that are essential or important for maintaining critical societal or economic activities. If you're unsure whether NIS2 applies to you, consult your national implementation of the directive.
You might already be conducting risk assessments for other frameworks like GDPR, ISO 27001, or general cybersecurity. Here's how NIS2 risk assessments differ:
| Aspect | NIS2 Risk Assessment | GDPR DPIA | ISO 27001 Risk Assessment |
|---|---|---|---|
| Primary Focus | Critical service continuity | Personal data protection | Information security |
| Scope | Critical services and their dependencies | High-risk personal data processing | All information assets |
| Impact Focus | Service disruption, societal impact | Rights and freedoms of individuals | CIA (Confidentiality, Integrity, Availability) |
| Frequency | Annually + when significant changes | When required for high-risk processing | Regularly (at least annually) |
| Mandatory Reporting | To authorities if required | To supervisory authority in some cases | Not mandatory |
The good news is that much of the work overlaps. If you already have ISO 27001 risk assessments, you can reuse significant portions for NIS2, though you'll need to ensure critical services are specifically addressed.
Here's the comprehensive process for conducting a NIS2-compliant risk assessment. We'll use a fictional water utility company, "AquaTech Services," to illustrate each step.
Start by identifying which services your organisation provides that are critical—those whose disruption would have significant negative consequences for society, the economy, or public safety.
Example - AquaTech Services identifies:
For each critical service, document:
For each critical service, map out all the IT systems, OT (Operational Technology) systems, processes, and assets that support it.
Example - For AquaTech's water supply service:
| System Type | Specific Systems | Function |
|---|---|---|
| SCADA Systems | WaterControl Pro v8.2 | Monitors and controls water treatment plants |
| Sensors/IoT | Flow meters, pressure sensors, quality monitors | Real-time water quality and distribution data |
| Network Infrastructure | Industrial network, wireless links to remote stations | Connects plants, pumping stations, and control centre |
| Business Systems | Asset management software, maintenance scheduling | Tracks infrastructure health and planned maintenance |
| Communication Systems | Emergency notification system, internal comms | Alerts during incidents and coordinates response |
This creates your "value chain" from critical service down to individual technical components.
Identify what your critical systems depend on—both within your organisation and from external providers.
Example - AquaTech's SCADA system dependencies:
This step is crucial because NIS2 specifically requires you to address supply chain security. A vulnerability in a critical supplier can be just as damaging as one in your own systems.
Read more about vendor audits and assessments.
For each system and dependency, identify realistic threats that could disrupt it. Consider both cyber and physical threats.

Example threats to AquaTech's SCADA system:
Don't just think about sophisticated cyberattacks—simple mistakes like misconfigured systems or unpatched software cause many real-world incidents.
For each identified threat, assess:
Use a consistent scale, typically 1-5 or Low/Medium/High/Very High.
Example - AquaTech assesses ransomware threat:
Threat: Ransomware attack on SCADA servers
Probability: Medium (3/5)
Reasoning: Water utilities are increasingly targeted. We have some protections but not comprehensive endpoint security on all industrial systems.Impact: Very High (5/5)
Reasoning: Would prevent remote monitoring and control of water treatment. Manual operation possible but significantly degraded. Could affect water quality monitoring. Estimated recovery time: 3-7 days.Risk Level: High (3 × 5 = 15)
Consider impact across multiple dimensions:
For each risk, decide how to treat it:
For high-priority risks, create detailed action plans.
Example - AquaTech's ransomware mitigation plan:
Risk: Ransomware attack on SCADA (Risk Level: High)
Treatment: Mitigate
Actions:
- Deploy endpoint detection and response (EDR) on all SCADA servers (Q1 2026)
- Implement application whitelisting on industrial systems (Q1 2026)
- Segregate SCADA network from corporate network with firewall (Q2 2026)
- Establish offline backups of SCADA configuration (Q1 2026)
- Conduct security awareness training for operators (Ongoing)
- Test backup restoration quarterly (Ongoing)
Target Risk Level: Medium (after controls)
Owner: IT Security Manager
Budget: €85,000
This creates a clear roadmap for improving your security posture based on actual risks to critical services.
NIS2 requires that you document your risk assessment and keep it up to date. This documentation should include:
The assessment isn't a one-time exercise. You must:
Using risk management software can help automate tracking and ensure nothing falls through the cracks.
The NIS2 Directive requires regular risk assessments, but doesn't specify an exact frequency. Best practice is:
Some organisations use a rolling review approach, assessing different critical services each quarter so the entire organisation is covered annually without overwhelming resources.

Based on observing many organisations implementing NIS2, here are pitfalls to avoid:
1. Being Too Generic
Don't just list generic threats like "ransomware" or "DDoS." Be specific to your systems and context. "Ransomware targeting SCADA servers running Windows Server 2019 in the water treatment plant" is much more useful.
2. Ignoring OT/Industrial Systems
Many organisations focus heavily on IT systems and overlook operational technology. If you operate industrial processes, these systems are often the most critical and may have unique vulnerabilities.
3. Forgetting Supply Chain Dependencies
A sophisticated risk assessment of your own systems means nothing if a critical cloud provider or software vendor is compromised. Always map and assess your key dependencies.
4. Assessing Impact Unrealistically
Be honest about impact. Don't downplay risks to make your organisation look better. The point is to genuinely understand where you're vulnerable so you can protect what matters most.
5. Creating a "Shelf Document"
The worst outcome is a risk assessment that looks great on paper but doesn't drive actual security improvements. Make sure action plans have owners, budgets, and deadlines, and track them to completion.
6. Not Involving the Right People
Risk assessments shouldn't be done in isolation by security teams. Involve:
You don't need to start from scratch. Several resources can help:
Risk Assessment Frameworks:
Software Tools:
Read more about when you need compliance software for risk management.
Your risk assessment isn't isolated—it should inform other aspects of your NIS2 compliance:
Think of risk assessment as the foundation that supports all other security activities.
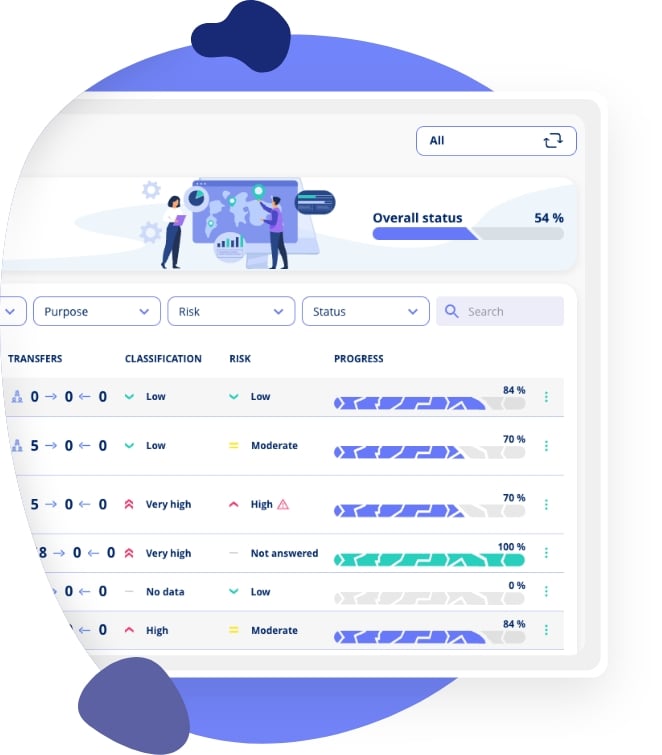
At .legal, we've built our Frameworks module specifically to support NIS2 compliance, including risk assessment:
Book a demo to see how we can streamline your NIS2 risk assessment process.
Once you've completed your NIS2 risk assessment, the real work begins—implementing the controls and mitigations you've identified. Here's what to do next:
Remember, NIS2 compliance isn't just about checking boxes—it's about genuinely protecting the critical services that society depends on. A thorough risk assessment helps you focus your security efforts where they matter most.
A NIS2 risk assessment is a systematic process of identifying, analysing, and evaluating cybersecurity risks to your critical services. It focuses on how cyber incidents could disrupt your service delivery to end users and what measures you need to reduce that risk to acceptable levels.
NIS2 risk assessments should be reviewed at least annually and updated whenever there are significant changes to your IT environment, services, threat landscape, or after a security incident. Regular reviews ensure your risk picture stays current and actionable.
Management bears ultimate responsibility for NIS2 risk assessments. In practice, the CISO or IT security team conducts the assessment, but management must approve the risk acceptance criteria, review results, and ensure adequate resources for risk mitigation.
NIS2 does not mandate a specific methodology. Common approaches include ISO 27005, NIST Risk Management Framework, and OCTAVE. The key is to use a structured, repeatable process that identifies threats, vulnerabilities, and impacts to your critical services systematically.
Both follow similar principles, but a NIS2 risk assessment specifically focuses on risks to network and information systems supporting critical services and their impact on service delivery. ISO 27001 risk assessments are broader, covering all information assets. A NIS2 assessment may require additional focus on supply chain risks.
Map your organization's services that fall under NIS2 sectors, determine which services would have significant impact on users or society if disrupted, identify the IT systems and networks supporting those services, and document the dependencies between services and systems.
A NIS2 risk register should contain identified risks with descriptions, likelihood and impact ratings, affected critical services and systems, current controls in place, residual risk levels, risk owners, and planned mitigation actions with timelines.
Identify your critical suppliers and their access to your systems, evaluate their security posture, assess the impact of supplier compromises on your services, include contractual security requirements, and monitor supplier security status on an ongoing basis.
NIS2 Article 21 requires measures including risk analysis policies, incident handling procedures, business continuity and crisis management, supply chain security, network security, vulnerability handling, cybersecurity hygiene practices, cryptography policies, access control, and multi-factor authentication.
Yes, if you have existing risk assessments from ISO 27001 or other frameworks, these can form the foundation. You will need to ensure they specifically cover NIS2 elements including critical service impact, supply chain risks, and alignment with Article 21 requirements.
Risk assessment is a cornerstone of NIS2 compliance. Complement your understanding with our articles on NIS2 training requirements, ISO 27001 alignment, and the directive fundamentals.












.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.