Information Security Management › ISAE
Becoming Compliant: .legal's ISAE 3000 & ISAE 3402

These days, every business uses suppliers to handle parts of their operations, whether cloud platforms, accounting software, HR services, consultants or IT management. It’s both efficient and necessary to outsource tasks to suppliers, but every time you outsource a task, new risks come into play because while you can outsource the work, you cannot outsource the responsibility.
It’s better to view your outsourcing as an extension of your own organisation. If a security breach occurs at one of your suppliers, it can have direct consequences for you, both in terms of operations and legal obligations.
So, auditing your suppliers is good practice and an essential control mechanism to ensure that your own responsibilities are not undermined by insecure practices on their side. Oversight is what gives you insight into how the supplier manages IT security and whether they are complying with the terms of your contract. If you don’t do this, you have no real way of knowing if the risks are being handled properly.
This article goes through how to organise and carry out audits of your suppliers’ IT security, whether you work in a small business with just a few suppliers or a larger organisation with more complex supplier relationships.
The purpose of auditing is to make sure that your suppliers are complying with the agreed security measures, contractual obligations and legal obligations, which your organisation is also subject to under GDPR, NIS2 or possibly even the ISO27001 standard, for example.
This means your business needs to establish and operate a structured process for auditing and controlling your suppliers’ IT security: from due diligence and contract signing to ongoing audits and the eventual end of the contractual agreement, as part of structured contract management.
Failing to audit your suppliers can have serious consequences, including data breaches, operational losses, fines from regulators, loss of trust from customers and partners and potential contractual or financial losses.
Several regulations and industry standards, such as GDPR, NIS2 and the ISO27001 standard, require you to audit your suppliers.
GDPR sets out clear rules on how organisations must handle their data processors, not only upon signing the contract but also during ongoing cooperation. The key point is that you, as the data controller, must maintain control even if personal data is handled by an external supplier. This means having written data processing agreements in place, applying suitable security measures and ensuring your supplier handles any security breaches properly and promptly.
It is also important to pay attention if your supplier processes data outside the EU. In such cases, GDPR requires that you have the necessary safeguards in place.
All of this is a central part of managing data processors. If you want to explore how to audit them in more detail, we recommend reading our separate article on the topic.
With NIS2, the EU has raised the bar for how organisations classified as critical infrastructure must handle IT security. This now includes your supply chain and, therefore, your relationships with suppliers and subcontractors. It is no longer enough to simply manage your own staff and systems. You must also be able to document why and how you set requirements for your suppliers and how you audit them.
You need to assess the risks linked to the supplier’s service, especially how those risks could affect the delivery of your own critical services.
This begins with having a clear overview of your suppliers and assessing the risk associated with each one. You must then ensure that your contracts reflect those risks and that your suppliers and their subcontractors are actually meeting the requirements in practice; this must be verified through your auditing.
Article 23 of NIS2 also states that management is responsible for overseeing and approving the organisation’s risk management, including the handling of supplier-related risks.
The ISO27001 standard sets requirements for how organisations should manage information security, including tasks that have been outsourced to suppliers. Risks related to external parties must be assessed and managed just like internal risks. You need to know what assets suppliers have access to, how access is controlled and how their handling of information and systems is audited.
The controls of the standard cover setting requirements in contracts, managing access to information and systems, auditing the supplier’s security level and handling changes in the delivery. You also need to consider the security of the entire supply chain and ensure that subcontractors meet the same requirements.
Security controls no. 5.19 to 5.23 in ISO27001:2022 cover these areas and form the foundation for structured supplier audits.
Supplier management starts with selecting suppliers and ends only when the task and all associated obligations have been completed. Auditing of suppliers can take place before, during and after the relationship.
Read more about what vendor contracts must contain. It is also part of implementing contract management in your organisation.
Before you outsource a task to a supplier, you should carry out a risk assessment of the task. This helps you define suitable security requirements for the supplier. These could include access control, encryption, incident handling, auditing and documentation. This is also the stage where you define your right to audit the supplier and possibly even their subcontractors. It often requires collaboration with procurement, legal and other business areas to ensure the requirements are both legally and practically anchored.
Once the cooperation is underway, your audit is about ensuring that the supplier complies with the agreed requirements and that these are suited to their risk profile.
The risk profile depends on whether the supplier has access to sensitive data or provides critical services. This should also be reflected in the required security measures.
Your audit can be carried out through document reviews, status meetings, third-party assessments of the supplier or by visiting them yourself to check that the agreed conditions are being followed.
It is also important to act if the supplier changes systems, processes or other parts of their organisation because these changes can affect security. The supplier should be required to notify you of such changes. This should be set out in the contract and is also something that should be audited.
Auditing might include checking how the supplier manages access control, uses encryption, handles software updates, conducts IT security awareness training and deals with incidents. Another relevant aspect is to review the supplier’s documentation, such as ISO certificates, internal audits or assurance reports, such as ISAE 3402. At the same time, you should find out whether the supplier uses subcontractors and how they are held to the same requirements so that you can trust that the entire supply chain is secure.
When the contract and cooperation come to an end, you need to make sure that the supplier’s access, data processing and so on are properly closed down. This might also involve an audit to confirm that the contractual terms for ending the cooperation have been followed.
Your auditing approach should reflect your organisation’s resources and complexity. A small organisation and a large organisation will have very different needs and possibilities when it comes to supplier management.
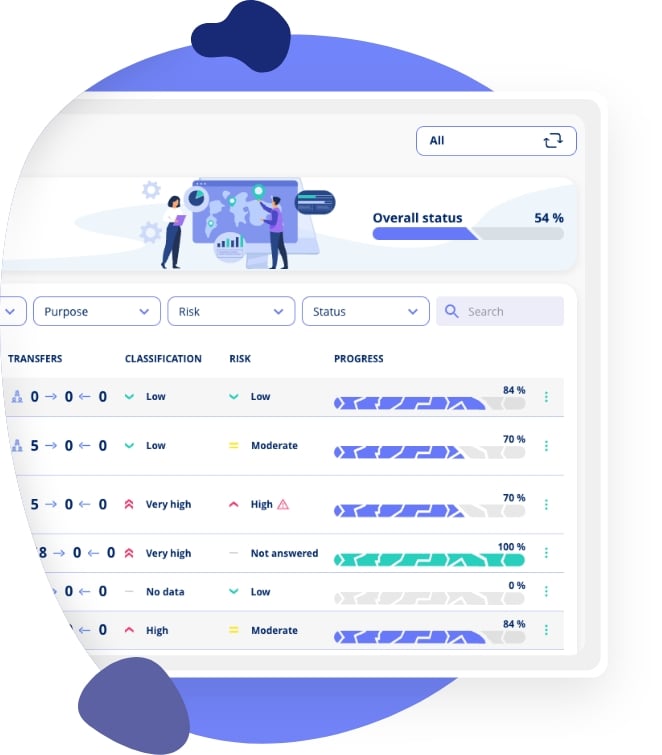
In smaller organisations, auditing is often handled by one person who also has many other responsibilities. In that case, it is important to prioritise and focus on the few suppliers who pose the greatest risk. Assessments and audits can be documented using simple templates or spreadsheets. Vendor management software can also be useful to give structure and an overview and help one person get more done.
In larger organisations, there are usually more suppliers, more system owners and higher demands around governance and documentation. Supplier management should be a dedicated role or function with links to IT, compliance, legal and procurement. Suppliers should be placed into risk categories, with the frequency and depth of audits adjusted accordingly. For the most critical suppliers, annual audits might be needed, while lower-risk ones may only require a simpler follow-up.
Vendor management software should be used to handle the complexity of dealing with all the different suppliers, contracts, requirements, audits, documentation and coordination across business areas.
Auditing suppliers gives you clarity, improves security and shows that your business is in control.
Start by getting an overview of your suppliers, carrying out risk assessments and making sure that the key requirements are written into your contracts. Use a simple tool to follow up and make audits a regular part of your security work.
Auditing suppliers' IT security is essential because your organisation's security is only as strong as its weakest link. Suppliers with access to your data or systems can introduce vulnerabilities, and regulatory frameworks like GDPR hold you responsible for how third parties handle your data.
A supplier IT security audit typically involves sending security questionnaires, reviewing certifications and compliance reports, assessing their security policies, evaluating their incident response capabilities, and potentially conducting on-site assessments or penetration testing.
It should cover access controls, data encryption, incident response plans, business continuity, employee training, physical security, vulnerability management, compliance certifications, data handling practices, and sub-processor management.
Supplier audits should be performed at least annually for critical suppliers and every two years for lower-risk suppliers. Additional assessments should be triggered by significant changes, security incidents, or contract renewals.
Key certifications include ISO 27001 (information security), SOC 2 Type II (service organisation controls), ISAE 3402 (service organisation assurance), and industry-specific certifications relevant to your sector.
Vendor risk management is the process of identifying, assessing, monitoring, and mitigating risks associated with third-party suppliers. It includes initial due diligence, ongoing monitoring, contractual requirements, and incident response coordination.
GDPR requires data controllers to only use processors that provide sufficient guarantees for data protection (Article 28). This means organisations must conduct due diligence on suppliers handling personal data and include specific contractual provisions.
Key questions include how they protect data, their encryption practices, access control policies, incident response procedures, employee training programs, compliance certifications, sub-processor usage, and data breach notification processes.
Prioritise based on the level of access to your data, the sensitivity of data they handle, their criticality to your operations, the volume of data processed, and any previous security incidents or concerns.
If a supplier fails an audit, document the findings, communicate concerns clearly, establish a remediation plan with deadlines, schedule a follow-up assessment, and consider whether to continue the relationship or find alternative suppliers.
Explore our guides on vendor risk management, supplier assessments, and how to build a robust third-party security programme.
















.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.