
Contract Management ›
What is Contract Compliance? A Practical Guide

Most businesses have vendor contracts. But in practice, many discover they have no real idea what those contracts contain, when they expire, or whether they meet today’s legal requirements.
That gap has grown alongside the regulatory landscape. GDPR, NIS2, and ISO 27001 all place specific requirements on what a vendor contract must contain and document. Getting it wrong can be costly — and vendor problems tend to surface at the worst possible moment.
This guide gives you the complete picture: what the contract must cover, what the law requires, and how to make sure you actually have it under control.
A vendor contract is a legally binding agreement between a business and an external supplier. It sets out the services, responsibilities, obligations, and terms of the relationship.
It is important to understand what a vendor contract is not: it is not the same as a Data Processing Agreement (DPA). The vendor contract governs the entire business relationship. The DPA is a separate legal requirement under GDPR, specifically regulating the processing of personal data. Both are necessary when the vendor processes personal data on your behalf — and one does not replace the other.
A good vendor contract creates clarity for both parties, documents your security and legal requirements, and gives you the means to act quickly if the relationship breaks down.
This is the question most people are looking for an answer to. And the answer is not a single clause — it is a checklist that covers the entire relationship from start to finish.
| Element | What it covers |
|---|---|
| Parties and subject matter | Who is the agreement between, and precisely what is being delivered? |
| Scope of services and SLA | Quality requirements, delivery timelines, uptime, and service levels |
| Price, payment, and adjustments | Fees, payment terms, price escalation, and billing model |
| Duration and termination | Contract term, notice periods, and conditions for automatic renewal |
| Liability and limitation | Who bears responsibility, and what is the cap on liability? |
| Confidentiality and non-disclosure | What information is confidential, and for how long? |
| Sub-contractors | Who are approved sub-contractors, and under what conditions? |
| Security requirements | Minimum technical requirements, certifications, and audit rights (NIS2 and ISO 27001-relevant) |
| Data processing | When is a DPA required? Link to GDPR Article 28 obligations |
| Breach and termination for cause | Consequences of contract breach and the right to immediate termination in serious cases |
| Exit strategy and data handling | What happens to data and systems when the contract ends? |
| Governing law and jurisdiction | Which law applies, and which court handles disputes? |
That is a long list. Deliberately so. A vendor contract that only covers the first four items is not a proper vendor contract — it is an offer with a signature.
There is one misunderstanding we encounter repeatedly: that a Data Processing Agreement replaces the vendor contract. It does not.
The two documents serve different purposes. The vendor contract governs the entire business relationship — services, pricing, liability, and termination. The Data Processing Agreement specifically governs the processing of personal data under GDPR Article 28. Both documents are required when your vendor processes personal data on your behalf.
GDPR also requires you to carry out oversight of your data processors and to ensure that any sub-processors are approved and bound by equivalent obligations. This is an area many organisations overlook — and it can create problems in the event of a data breach.
A practical rule of thumb: if your vendor has access to personal data for which you are the controller, a DPA is required alongside the vendor contract. The two agreements are linked, but they are separate documents with distinct purposes.
This is where .legal’s approach differs from most. NIS2 is not only relevant for organisations directly in scope — it affects the entire supply chain.
NIS2, implemented in Danish law on 1 July 2025, sets explicit supply chain security requirements under Article 21(2)(d). Organisations within the in-scope sectors must actively manage security across their supply chains. And that happens primarily through contracts.
In practice, the vendor contract must include:
A practical example: an organisation in the energy sector uses a cloud provider for business-critical systems. Under NIS2, it is not sufficient to know the provider takes security seriously. It must be in the contract — which standards are maintained, how incidents are reported, and what happens if the relationship ends.
Organisations not directly in scope can still be affected: if you supply services to a NIS2-covered customer, expect them to pass security requirements down to you contractually. That is the cascade effect built into NIS2’s supply chain logic.
Read more about NIS2 and what it requires of your organisation.
ISO 27001:2022 addresses supplier security directly through two controls:
For organisations that are certified or working towards ISO 27001 certification, vendor contracts form part of the audit evidence reviewed during certification assessments. Having an internal security policy is not enough — it must be reflected in the contracts you hold with your vendors.
Financial organisations under DORA (the Digital Operational Resilience Act) face equivalent obligations under Article 30, which sets specific contractual requirements for ICT service providers — including exit strategies, inspection rights, and reporting obligations.
Read more about ISO 27001 compliance and what it requires in practice.
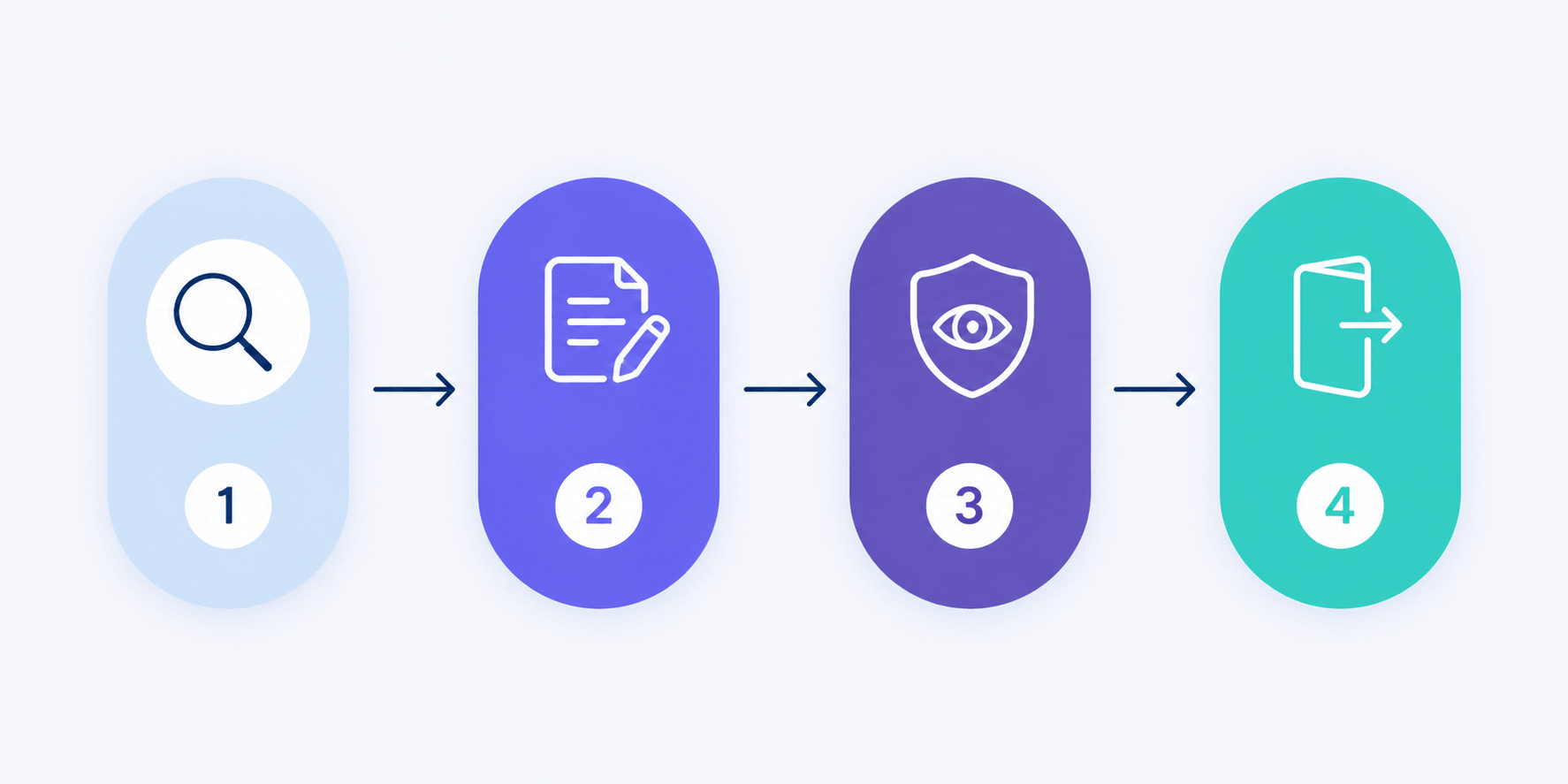
The contract is the starting point, not the finish line. A solid vendor contract creates the framework — but managing vendor risk is an ongoing process.
A structured approach looks like this:
It sounds straightforward. But for organisations managing 20, 50, or 200 active vendor contracts, it is a genuine governance challenge to track expiry dates, verify that security requirements are still current, and document oversight for regulators.
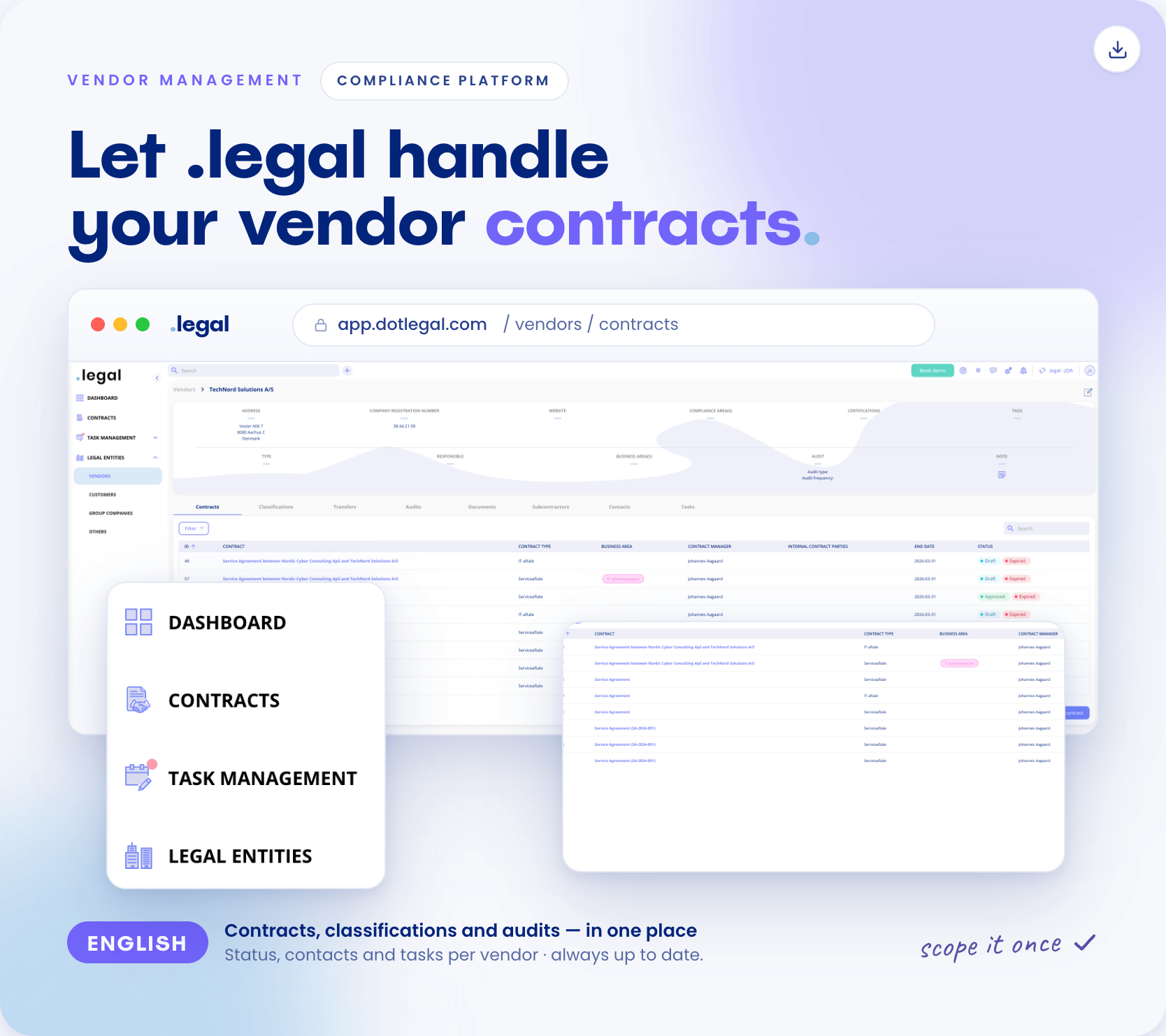
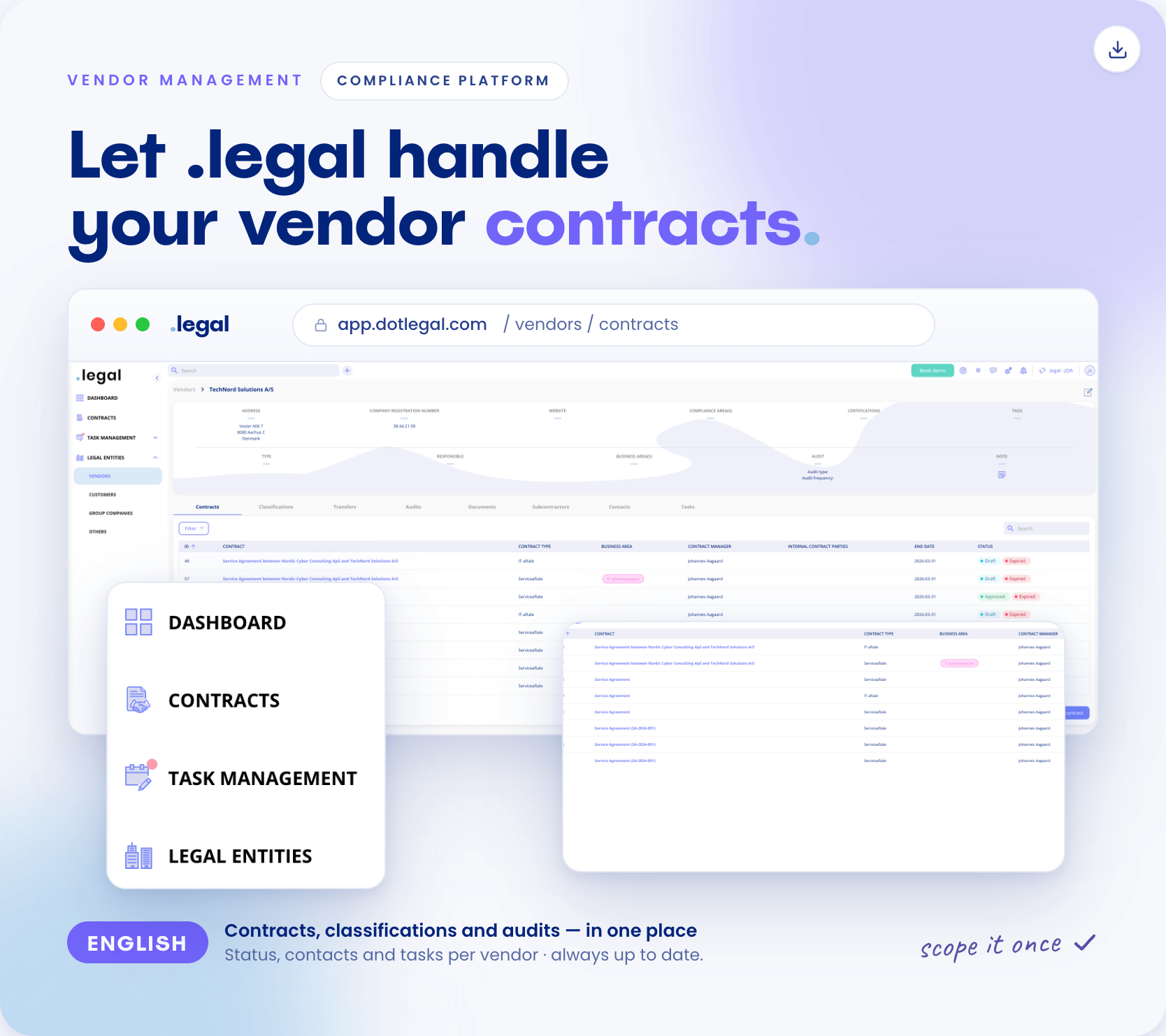
That is exactly what .legal’s vendor management module addresses: a central view of all vendor relationships, with linked contracts, DPAs, audit logs, and automatic reminders for renewal and follow-up.
Read more about information security risk management and vendor audits.
These mistakes are more common than you might expect. And most are only discovered when something goes wrong.
For organisations with a significant number of vendor relationships, ad hoc management is not sustainable. What is needed is a structured system.
A good setup includes:
.legal’s contract management software is built for precisely that: oversight, reminders, and integration with the compliance process. Want to see how it works in practice? Book a free demo and get a clear picture of what is missing in your vendor management.
A vendor contract governs the entire business relationship — services, pricing, liability, and termination. A DPA specifically governs the processing of personal data under GDPR Article 28. Both are required when the vendor processes personal data. One does not replace the other.
At minimum: the parties, scope of services, price and payment, duration and termination, confidentiality, and liability. If the vendor processes personal data, a DPA must be attached under GDPR Article 28. The contract should also regulate the use of sub-contractors.
NIS2 Article 21(2)(d) requires organisations in in-scope sectors to manage supply chain security contractually. Contracts must include specific security requirements, audit rights, incident response obligations with defined timeframes, and an agreed exit strategy.
At expiry, following changes in legal requirements, after a vendor security incident, or when the scope of services changes materially. Critical vendor contracts should be reviewed at least annually.
The exit strategy should be agreed in the contract upfront: the vendor returns or deletes data within a defined timeframe, access is revoked, and deletion is documented. This is required under GDPR Article 28 and expected under NIS2 and ISO 27001.
Typically the person who enters into agreements — procurement manager, legal counsel, COO, or CFO. Compliance and DPO functions should be involved when the contract involves personal data or security requirements.
No. GDPR Article 28 sets specific requirements for a DPA that a standard vendor contract does not cover. Both documents are required when the vendor processes personal data on your behalf.
Annex A.5.19 and A.5.20 require security requirements to be documented in vendor agreements — covering confidentiality, incident notification, access control, audit rights, and exit terms. For certified organisations, vendor contracts form part of the audit evidence.
Vendor risk covers operational, security, and compliance risk from depending on external parties. A structured approach includes due diligence before signing, clear security requirements in the contract, and ongoing oversight.
It requires a central contract repository with automatic renewal reminders, linked DPAs, and an audit log. .legal's vendor management and contract management software handles exactly that. Book a demo to see it in practice.
Explore more guides on contract management, data processing agreements, vendor audits, and how to bring vendor compliance under one roof.









.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.