
NIS2 › NIS2 Compliance
NIS2 Introduction

NIS2 requires that both management and employees in covered organisations receive proper training in cybersecurity.
This article examines the training requirements in NIS2, including who must be trained, what the training should contain, and tips for getting started.
You can read our introduction to NIS2 if you want an overview of the directive.
NIS2 places particular responsibility on management's involvement in steering the organisation's cybersecurity efforts, and therefore it is both a good idea and a requirement that members of management must have the necessary knowledge, which can come through participation in relevant cybersecurity courses. This ensures that management has a stronger professional foundation for managing these risks.
At the same time, NIS2 requires that measures include basic cyber hygiene practices and cybersecurity training, which employees must therefore be educated in.

This requirement must be met continuously, which means that you cannot simply ask relevant employees to take a one-off course. You must instead ensure that everyone in the organisation has skills in 'basic cyber hygiene practices'. Therefore, the organisation should establish a plan for how knowledge and behaviour are developed and maintained over time.
So there is both a NIS2 requirement for training for managers and the organisation as a whole, and that everyone has the necessary knowledge and practice in cybersecurity to fulfil their roles.
To comply with NIS2, management must have sufficient knowledge of cybersecurity so they can make qualified decisions about it. NIS2 therefore requires that members of management acquire knowledge and skills, for example through relevant courses on managing cybersecurity risks. There are no rigid requirements for how this should be met. What's important is that management as a whole gains the competencies to understand cybersecurity threats, assess the organisation's risks, and make qualified decisions on the subject.
For example, it would be appropriate for management to be trained in general IT security courses, risk management, relevant legal requirements in the IT area, and relevant IT security standards.
NIS2 does not establish detailed requirements for the form and content of training, but it is important that training is seen in the light of NIS2, which concerns cybersecurity in critical infrastructure, and in light of the management requirements NIS2 sets regarding governance.
It is employees who work daily with systems, data, and communication, and who are therefore also the most important in the organisation's daily cybersecurity efforts. NIS2 therefore also emphasises that cybersecurity is about behaviour and competencies in individual employees.
Management should encourage employees to receive corresponding training, meaning that employees also receive education that corresponds to their role in the organisation, which may therefore be different from management's training.
For example, you can educate employees with awareness training, which all employees complete, and which lays a foundation for employees' awareness and knowledge of cybersecurity. This can happen through an e-learning course that explains the most common threats such as phishing and other social engineering attacks, password security, information sharing, and physical security.
Training must be understandable and relevant to everyone with responsibility for delivering the critical service to end users. This can be operational staff who have direct access to production facilities, or administrative staff with access to central systems, as well as anyone with access to the organisation's facilities.
You should ensure that staff with particular responsibility for the delivered service, such as operational staff or IT, receive training that aligns with the risk assessment. Critical personnel should therefore have targeted training, as their work entails greater risk for service delivery.
Targeted training can also take place as e-learning courses with specialised courses, or with internal workshops on the topics, or through participation in external training courses. What's most important is that employees are continuously trained so they can each handle the risks that the organisation and sector face.
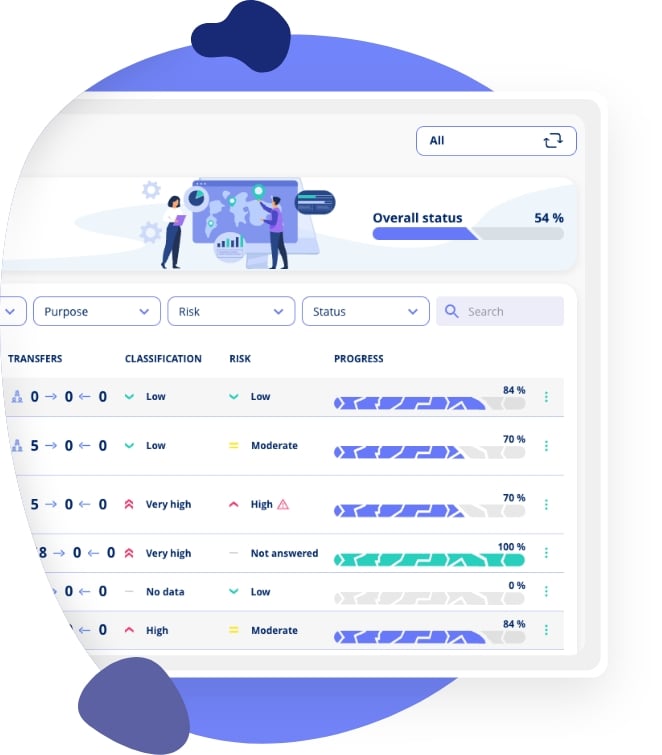
| Employee Group | Training Needs | Examples |
|---|---|---|
| Management | Strategic cybersecurity, governance, risk management | Executive courses, ISO 27001, workshops |
| All employees | Basic cyber hygiene, phishing, passwords | Awareness training, e-learning |
| IT personnel | Technical cybersecurity, incident response, network security | Certifications, technical courses |
| Operational staff | Operational security, physical security, procedures | Targeted workshops, on-the-job training |
| HR & Administration | Data protection, confidential information, social engineering | GDPR courses, awareness training |
Training must be documented, for example with a course certificate or written confirmation of participation, so it can be provided to authorities during inspection.

If you choose to conduct your own training courses, you can create a participant list, describe the learning objectives and course content, and save the training materials. It doesn't need to be complicated.
Use information security software to keep track of documentation and ensure all employees are up to date with their training.
NIS2's requirements for the organisation's cybersecurity training are significant, and therefore it is also a good idea to take a structured approach to the requirement by creating a training policy or plan.
Your training policy can describe the different employee groups and their tasks. You can use this to provide targeted training, so that tasks involving greater risks receive targeted training.
You should specify the purpose of training for each employee group, and then organise their training accordingly, such as content, frequency, tests, and documentation.
The training policy doesn't need to be long, and should simply be used as operational help for training work, and it also functions as documentation.
If your organisation does not meet NIS2's training requirements, it can have consequences for management, who can be sanctioned, and additionally the organisation can receive a fine.
NIS2 involves personal management liability, which means that board members or directors can become personally liable in cases of gross negligence, including lack of cybersecurity training.
Fines for non-compliance can be significant:
In addition to financial sanctions, lack of training can also weaken the organisation's actual cybersecurity and increase the risk of security incidents.
NIS2 sets training requirements for both management and employees. Here's a practical approach to getting started:
Organise the organisation's training so it matches roles and needs, and describe all this in a training policy. This will make it easier to decide how the training requirement is continuously met, and adjust the training effort as needed.
At .legal, we can help you structure your NIS2 compliance, including handling training requirements and documentation. See how our Frameworks module supports NIS2 compliance or book a demo.
NIS2 requires training for both management bodies and all employees. Management must receive specific cybersecurity training to understand risks and assess cybersecurity measures. All employees must receive regular training to identify and respond to cyber threats relevant to their roles.
Management training should cover the organisation's threat landscape, NIS2 legal obligations and penalties, risk management frameworks, incident response procedures, their personal liability under NIS2, supply chain security, and how to evaluate cybersecurity investment decisions.
NIS2 does not specify exact frequency, but training should be regular and ongoing. Best practice is annual training for all staff with supplemental sessions when threats change, after incidents, for new employees, and when policies or systems are updated.
Employee training should include recognising phishing and social engineering, password security and multi-factor authentication, secure handling of data, incident reporting procedures, acceptable use policies, mobile and remote working security, and awareness of current threat trends.
Yes, NIS2 does not mandate a specific delivery format. Online training, e-learning platforms, in-person workshops, and blended approaches are all acceptable. The key requirement is that training is effective, documented, and reaches all relevant personnel.
Document your training programme including content descriptions, delivery schedules, attendance records, assessment results, and evidence that training is updated regularly. You should also document how training content addresses specific NIS2 requirements.
Inadequate training can lead to regulatory fines, but more importantly, management can be held personally liable under NIS2. Authorities can issue compliance orders, impose fines, and in severe cases, temporarily ban individuals from management positions.
Yes, training should be tailored to roles. Management needs strategic cybersecurity understanding, IT staff need technical security training, and general employees need practical awareness training. The depth and focus should match each role's responsibilities and risk exposure.
ISO 27001 also requires security awareness and training (Annex A 6.3). NIS2 training can build on ISO 27001 awareness programmes but must additionally cover NIS2-specific topics like incident reporting obligations, management liability, and sector-specific threats.
Use a combination of knowledge assessments (quizzes/tests), phishing simulations, incident response exercises, tracking of security incident trends, and regular competency reviews. Document results to demonstrate continuous improvement in your organisation's security culture.
Training is one piece of the NIS2 puzzle. Explore our guides on risk assessment methodology, how NIS2 compares to ISO 27001, and the directive fundamentals to build comprehensive compliance.













.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.