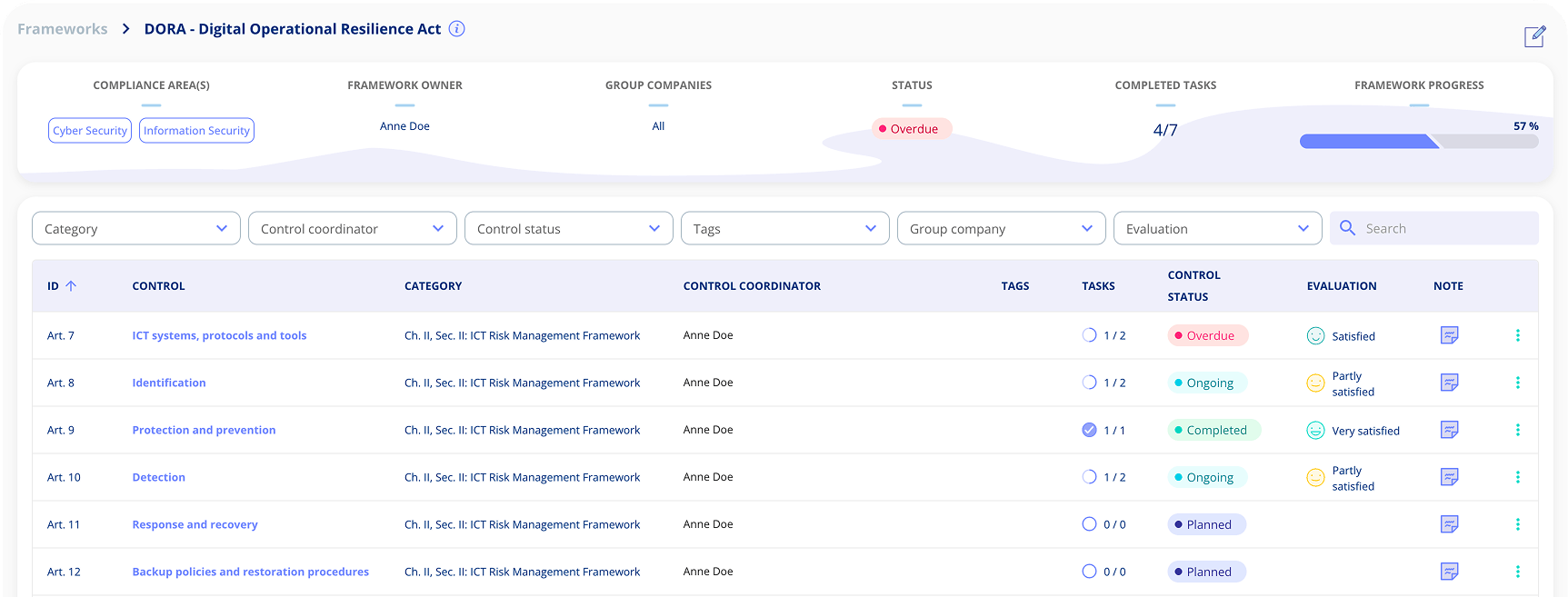
DORA FRAMEWORK A complete framework for digital operational resilience
The Digital Operational Resilience Act (DORA) is an EU regulation that establishes uniform requirements for ICT security across the financial sector. We have mapped all requirements from the five core pillars into clear, action-oriented frameworks with automated compliance tracking and integration with your existing security standards.
-
Complete DORA framework covering all five pillars of digital operational resilience
-
Select only requirements that apply to your entity type – proportionate compliance
-
Real-time compliance tracking shows exactly where you stand with DORA
-
Reuses existing ISO 27001, NIS2 and GDPR tasks – avoid duplicate work
DORA Framework DORA's Five Core Pillars:
Our DORA Framework covers the full regulation, structured around the five pillars that form the foundation of digital operational resilience for financial entities.
-
Pillar 1: ICT Risk Management (Articles 5–16)
Comprehensive governance framework for identifying, protecting against, detecting, responding to and recovering from ICT-related disruptions. Includes requirements for ICT risk management policies, digital operational resilience strategies and business continuity plans.
-
Pillar 2: ICT Incident Reporting (Articles 17–23)
Standardised incident classification, notification procedures and reporting timelines. Financial entities must classify ICT-related incidents, report major incidents to competent authorities and voluntarily report significant cyber threats.
-
Pillar 3: Digital Operational Resilience Testing (Articles 24–27)
Requirements for testing ICT systems including vulnerability assessments, network security testing and, for significant entities, threat-led penetration testing (TLPT) at least every three years. -
Pillar 4: ICT Third-Party Risk Management (Articles 28–44)
Framework for managing risks arising from ICT third-party service providers. Includes contractual requirements, concentration risk assessment and the EU Oversight Framework for critical ICT third-party providers. -
Pillar 5: Information Sharing (Article 45)
Voluntary arrangements for exchanging cyber threat intelligence and information among financial entities to enhance collective digital operational resilience.

DORA FRAMEWORK Tailor your DORA compliance strategy
DORA applies to virtually all regulated financial entities in the EU, but requirements are proportionate to the size, risk profile and complexity of each entity. Customise your compliance approach efficiently:
How to design your DORA framework:
-
Identify your entity type and applicable proportionality tier
-
Map relevant regulatory technical standards (RTS) to your operations
-
Focus on the pillars most critical to your risk profile
-
Assess ICT concentration risk and third-party dependencies
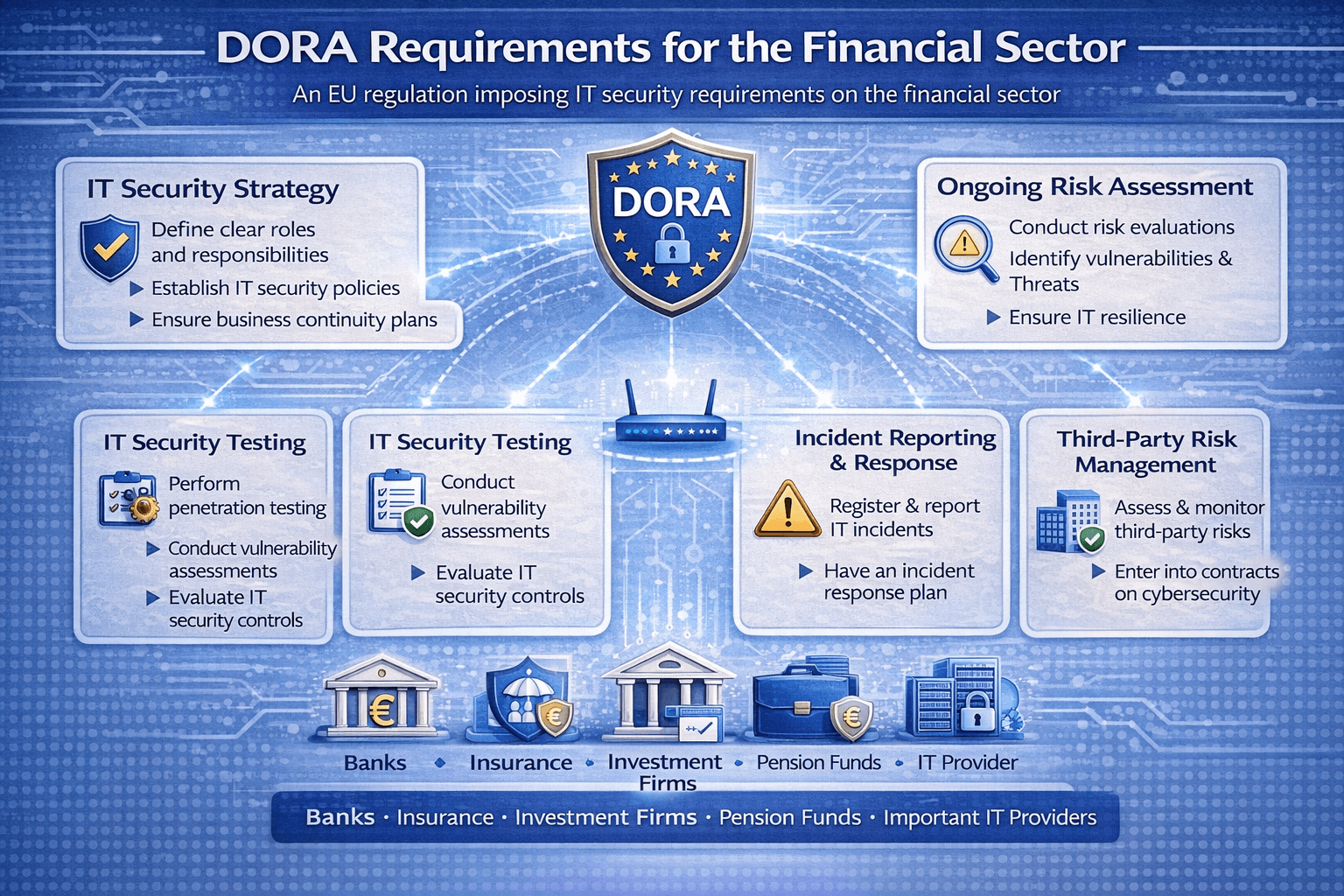
DORA Framework Who Must Comply With DORA?
DORA applies to 21 categories of financial entities, including banks, insurance and reinsurance companies, investment firms, payment institutions, electronic money institutions, crypto-asset service providers, central securities depositories, credit rating agencies, crowdfunding platforms and fund managers. It also covers ICT third-party service providers that deliver services to financial entities, including cloud service providers and data analytics providers.
Proportionality principle: Microenterprises (fewer than 10 employees and turnover/balance sheet below €2 million) benefit from a simplified ICT risk management framework under Article 16, while significant entities face additional requirements such as threat-led penetration testing.

DORA FRAMEWORK Leverage synergies with existing compliance frameworks
The DORA Framework integrates seamlessly with your existing compliance programmes. Many financial entities already hold ISO 27001 certification or comply with NIS2 – DORA builds on these foundations:
Framework Synergies:
-
Existing security controls satisfy multiple DORA requirements simultaneously
-
Documentation and processes can be reused across frameworks
-
Investment in one framework strengthens compliance on multiple fronts
-
60–70% overlap with ISO 27001 and NIS2 reduces implementation effort
Examples of overlapping frameworks:
-
ISO 27001
Information security management and risk assessment processes map directly to DORA's ICT risk management requirements. Annex A controls cover many of the same technical and organisational measures DORA demands.Go to framework -
NIS2
Network and information security requirements overlap significantly with DORA's incident reporting and risk management pillars. Financial entities subject to both can leverage shared controls and reporting processes.Go to framework -
GDPR
Data protection and breach notification obligations complement DORA's incident reporting requirements. Security of processing under GDPR aligns with DORA's ICT security measures.Go to framework
Our Customers
+400
companies
+10.000
users
+79.000
contracts
+14.000
processing activities

Bech-Bruun
Mikkel Friis Rossa (Partner)

Fenerum
Rasmus Boutrup (Financial Controller)

Lægeforeningen
Michael Berner (Lawyer)

Molecule Consultancy
Nanna Rodian Christensen (HR & Operational Manager)

Plum Safety
Ulrik Dueholm Beckmann (QC, CM og ESG Lead)

Bech-Bruun
Mikkel Friis Rossa (Partner)

Fenerum
Rasmus Boutrup (Financial Controller)

Lægeforeningen
Michael Berner (Lawyer)

Molecule Consultancy
Nanna Rodian Christensen (HR & Operational Manager)

Plum Safety
Ulrik Dueholm Beckmann (QC, CM og ESG Lead)

Novicell
Julie Oxenvad (Legal Consultant)

Min By Media
Tinna Schultz (HR Manager)

DMJX
Kaspar Rochholz (GDPR Coordinator)

Axel Kaufmann ApS
Julie Lundkvist Andreasen (Lawyer and Head of Costumer Service)

NRGi
Mette Mühlendorph (Compliance Specialist)

Novicell
Julie Oxenvad (Legal Consultant)

Min By Media
Tinna Schultz (HR Manager)

DMJX
Kaspar Rochholz (GDPR Coordinator)

Axel Kaufmann ApS
Julie Lundkvist Andreasen (Lawyer and Head of Costumer Service)

NRGi
Mette Mühlendorph (Compliance Specialist)
.legal Compliance Hub
Read all about .legals compliance on our compliance hub.
-
ISAE 3402
ISAE 3402 statementGet a copy of .legal A/S's latest ISAE3402 (type 2) IT security statement
-
ISAE 3000
ISAE 3000 statementGet a copy of .legal A/S's latest ISAE3000 (type 2) statement of our GDPR compliance
-
Data Processing Agreement (DPA)
Data processing agreementFind .legal A/S's data processing agreement here.
-
IT security
IT Security MeasuresAll .legal A/S's implemented and approved IT security measures are described here.
Frequently Asked Questions about DORA Framework
What is DORA (Digital Operational Resilience Act)?
DORA is an EU regulation (2022/2554) that establishes uniform requirements for ICT security across the financial sector. It entered into force on 16 January 2023 and has applied since 17 January 2025. Unlike a directive, DORA is directly applicable in all EU member states without national transposition.
Who must comply with DORA?
DORA applies to 21 categories of financial entities, including banks, insurance companies, investment firms, payment institutions, electronic money institutions, crypto-asset service providers, central securities depositories, credit rating agencies, crowdfunding platforms and fund managers. It also covers ICT third-party service providers that deliver services to financial entities.
What are DORA's five pillars?
DORA is built on five pillars: (1) ICT Risk Management – governance framework for managing ICT risks, (2) ICT Incident Reporting – standardised classification and reporting of major incidents, (3) Digital Operational Resilience Testing – including threat-led penetration testing for significant entities, (4) ICT Third-Party Risk Management – contractual and oversight requirements for ICT providers, and (5) Information Sharing – voluntary cyber threat intelligence exchange.
How does DORA relate to NIS2 and ISO 27001?
DORA shares significant overlap with both NIS2 and ISO 27001. Organisations with ISO 27001 certification typically have 60–70% of DORA requirements already covered. NIS2's incident reporting and risk management requirements also align closely with DORA's pillars. Financial entities subject to both DORA and NIS2 can leverage shared controls and reporting processes.
What is the proportionality principle under DORA?
DORA applies requirements proportionate to an entity's size, risk profile and complexity. Microenterprises with fewer than 10 employees and turnover or balance sheet below €2 million benefit from a simplified ICT risk management framework under Article 16. Significant entities face additional requirements such as mandatory threat-led penetration testing every three years.
What are the penalties for non-compliance with DORA?
DORA empowers competent authorities to impose administrative penalties and remedial measures. For critical ICT third-party providers, the EU Oversight Framework can impose periodic penalty payments of up to 1% of average daily worldwide turnover. Member states may set additional penalties through national legislation.




.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

+45 7027 0127 and I'll get you started
.legal is not a law firm and is therefore not under the supervision of the Bar Council.