
GDPR › GDPR Documentation & Compliance
Compliance Checklist: How to be GDPR Compliant

When your company passes personal data to a supplier (a data processor), you remain responsible for ensuring that the processor complies with the GDPR.
The GDPR states clearly that personal data must be handled responsibly at every stage of the supply chain. This ensures everyone's data, yours and mine, is protected correctly at all times. Simply outsourcing a business process doesn't remove your GDPR responsibilities.
Therefore, you must verify that your suppliers meet the GDPR standards required of you and provide the same level of data protection that your business expects.
This article explains why and how you should audit your data processors effectively.
The GDPR imposes specific rules on the relationship between the data controller (your business) and its data processors.
The rules require you to select only those data processors that offer sufficient guarantees they will handle personal data correctly under the GDPR.
Your data processors can't delegate their responsibilities to sub-processors without your prior approval. This ensures your personal data won't be handled insecurely by another party.
You must document any sharing of personal data with data processors in a Data Processing Agreement (DPA), clearly specifying your requirements.
The GDPR also requires you to demonstrate compliance actively. This means you must audit your data processors regularly, ensuring they fulfil their obligations under the DPA in practice.
Auditing of your data processors starts with clearly identifying all of them, providing a clear overview of your suppliers.
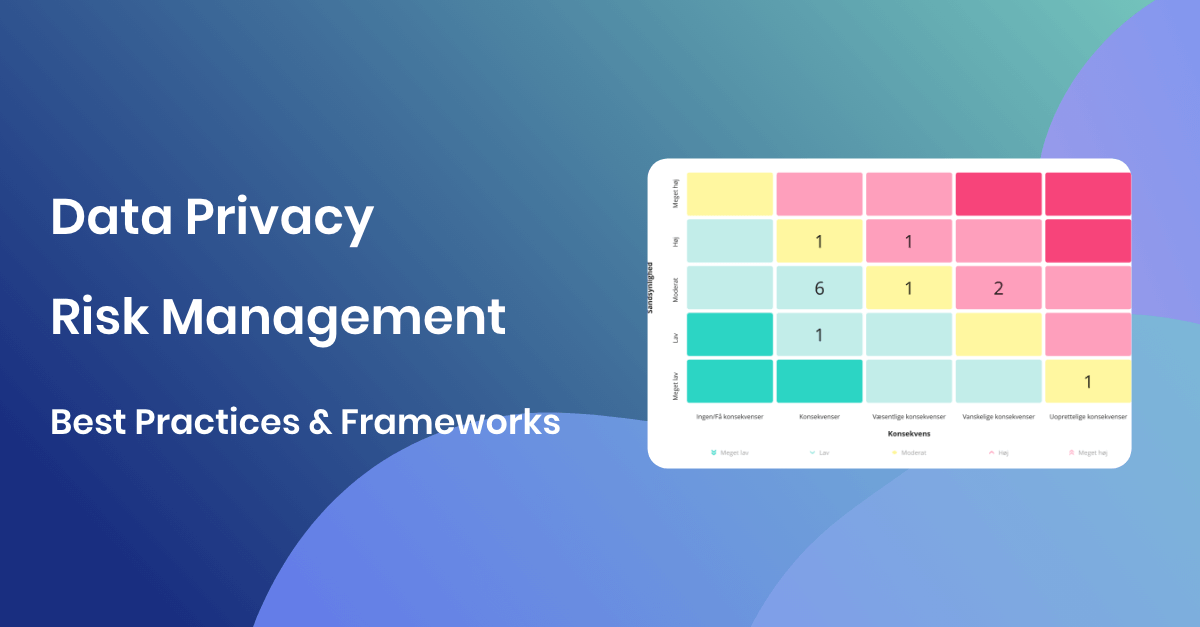
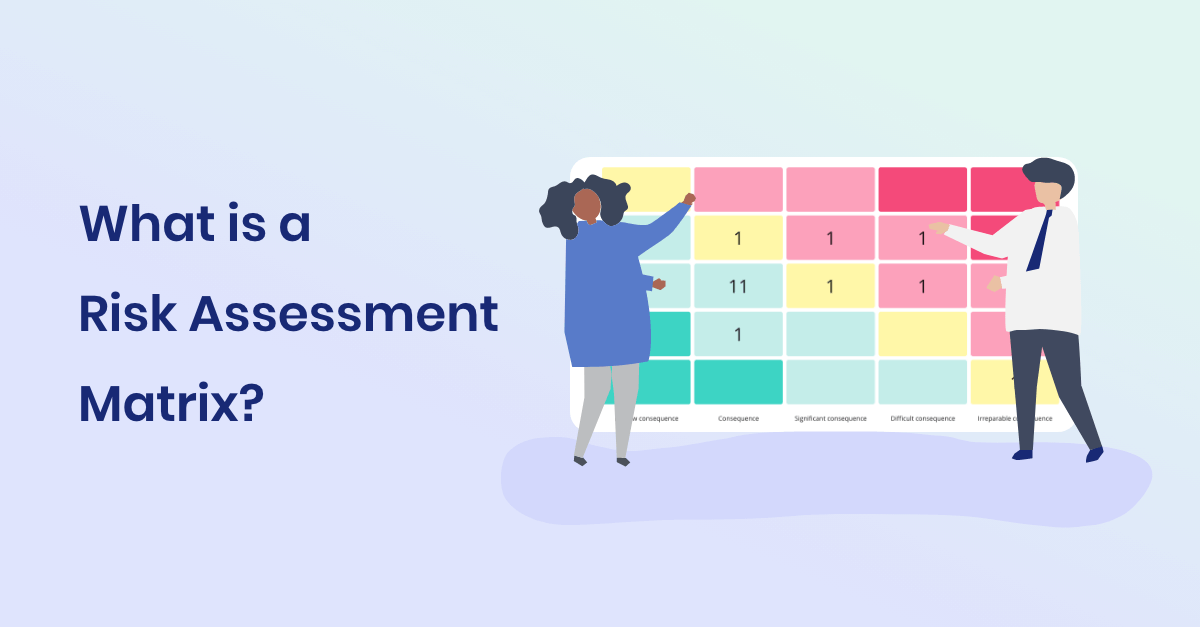
Once you’ve mapped them, conduct a risk assessment of each data processor. You can base your audit strategy on these risk assessments or use the simple method provided below.
The Danish Data Protection Agency (Datatilsynet) has created a guide to help you choose how to audit your data processors. It involves answering these four simple questions:
|
How many people’s data does the data processor handle?
|
|
Does the data processor handle sensitive personal data?
|
|
Does the data processor handle confidential personal data?
|
|
Is the data processor’s activity intrusive to the data subjects (e.g., profiling, combining datasets, surveillance)?
|
Results
Next, determine your audit method for each of your data processors by adding up the points from your four answers to the questions above.
The results from the questionnaire above reflect your risk level when outsourcing personal data processing to your data processors. A higher risk indicates you should choose a more thorough auditing approach.
Datatilsynet suggests these six auditing methods, which you can select based on your risk assessment:
If your data processor has established a strong reputation and proven itself as trustworthy, you may choose a reactive auditing approach. This means you only carry out an audit if you become aware of potential problems with the data processor.
For example, you might learn about issues through media coverage or reports from regulatory authorities. You may also notice operational difficulties with the data processor that prompt you to perform an audit.
If your data processor has a strong reputation, you can simply request written confirmation from them that they continue to comply with GDPR.
This confirmation can be a straightforward statement in which the data processor assures you that no changes have occurred in their procedures or security measures compared to your Data Processing Agreement.
If you later become aware of security breaches or negative media coverage, you can then contact the data processor to perform additional audits or ensure the issues have been resolved.
The data processor can provide an annual status report containing details of how they're complying with your Data Processing Agreement, including any changes made to their IT security, systems, or policies. This report can either be published on the data processor's website or sent directly to you.
It's important the status report clearly addresses the specific conditions outlined in your Data Processing Agreement, enabling you to effectively verify compliance with each requirement.
If your data processor follows an approved code of conduct (as per GDPR Article 40) or holds a relevant certification (as per GDPR Article 42), you can use this as evidence during your audit.
You should ensure the code of conduct or certification covers all requirements specified in your Data Processing Agreement. If some requirements are not covered, ask the processor for additional documentation proving compliance with these terms.
Additionally, request documentation detailing any personal data breaches that have occurred since your last audit, along with the measures implemented to prevent future incidents.
An independent third party can audit your data processor’s compliance with your Data Processing Agreement, for example, through an ISAE 3000 report issued by an auditor. External audits provide an objective assessment of whether the data processor meets the necessary requirements.
If you choose this approach, ensure the audit covers all areas relevant to your business and included in your Data Processing Agreement.
If the audit identifies gaps or risks, you should contact the data processor to ensure these issues are addressed.
You can also carry out an audit yourself by sending questionnaires, requesting documentation, or visiting the data processor in person. A physical audit allows you to verify directly whether security measures, such as IT security, access controls, and physical protection of servers and systems, match the agreed requirements in practice.
Fundamentally, your audit should focus on verifying compliance with the requirements in your Data Processing Agreement. These requirements vary depending on each individual agreement, as data processing activities differ, as do the types of companies providing these services, such as Microsoft or an external accounting firm.
This variability impacts what you should audit, but you should audit that the data processor:
Only process personal data according to documented instructions from you (the data controller).
Immediately inform you if any instructions given by you breach the GDPR.
Restrict access to personal data exclusively to employees who genuinely need access and who are bound by confidentiality obligations.
Have implemented appropriate technical and organisational security measures as required by GDPR Article 32, as well as any additional security measures specified by you.
Help you conduct risk assessments by providing relevant information about their data processing and security measures.
Perform their own risk assessment regarding processing done on your behalf and take steps to mitigate identified risks.
Comply fully with GDPR requirements when using sub-processors (as stated in Article 28, sections 2 and 4), and regularly audit these sub-processors.
Only transfer personal data to third countries on a lawful basis and can document the legality of these transfers.
Support you in managing requests from data subjects (e.g., requests for access, correction, or deletion).
Immediately notify you about any personal data breaches and assist you in reporting the breach to the Data Protection Authority within 72 hours.
Regularly provide GDPR, IT security, and data protection training to relevant employees.
Delete or return all personal data after termination of the Data Processing Agreement.
Imagine you have 18 data processors, and you have identified that you will need to apply three different audit methods to ensure they comply with your Data Processing Agreements.
Managing this manually is complex and time-consuming, making it natural to standardise and automate as much as possible.
Once you have completed the risk assessments for each data processor and chosen your audit approach, the next step is to standardise and automate your auditing process.
First, create audit templates. You can either prepare individual templates customised to each data processor for reuse each year or create general templates for each of the six audit methods.
Next, send out the audit requests to your data processors. You can set up a standard email to send these requests regularly (e.g., annually). Alternatively, create customised emails for each data processor, each including the specific auditing template you have prepared.
Finally, ensure you receive a timely response from each processor and verify that the information provided is complete and satisfactory.
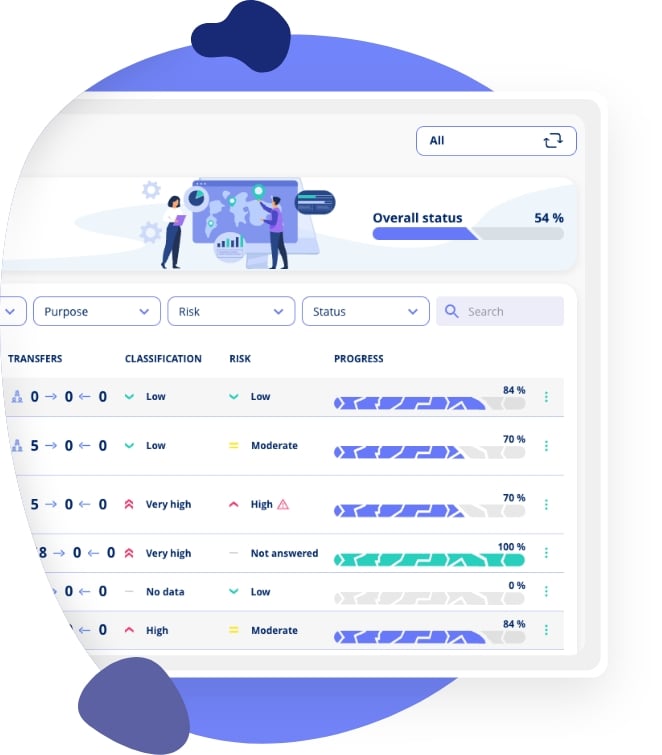
Using vendor management software gives you all the tools needed to automate the auditing of your data processors, as part of a structured contract management approach.
It helps you track risk assessments, manage audit templates, send and receive your audit requests, automatically handle reminders, and enables structured follow-ups. This is especially useful if responses from your data processors aren't satisfactory and require many follow-ups.
Additionally, all your audit activities are clearly documented within the software, simplifying your overall compliance documentation. Read more about what vendor contracts must contain.
If you would like to try this in practice right now, you can try the free version of a vendor management tool here.
The GDPR requires you to document your compliance with GDPR, which means documenting all your audit activities, including risk assessments of data processors, the audit results, communications with data processors about the audits, follow-ups, and the data processors’ overall compliance with GDPR requirements. See our step-by-step guide to implementing contract management.
A data processor audit is a systematic review of how a third-party supplier (data processor) handles personal data on your behalf. Under GDPR, as a data controller, you are required to verify that your data processors comply with the GDPR and your Data Processing Agreement. Audits can range from simple written confirmations to on-site inspections.
The frequency depends on your risk assessment. Higher-risk processors handling large volumes of data, sensitive personal data, or engaging in intrusive activities should be audited more frequently, typically annually. Lower-risk processors may be audited less often, but you should always monitor for any changes or incidents that warrant an immediate review.
The six methods are: (1) Reactive audits triggered by known issues, (2) Written confirmation from the processor, (3) Annual status reports, (4) Certifications and codes of conduct under GDPR Articles 40 and 42, (5) Independent third-party audits such as ISAE 3000 reports, and (6) Conducting your own audit through questionnaires, documentation review, or on-site visits.
An audit should verify that the processor only processes data per your documented instructions, restricts access to authorised personnel, implements appropriate technical and organisational security measures, complies with sub-processor requirements, lawfully transfers data to third countries, supports data subject requests, and notifies you of breaches promptly.
Yes. A Data Processing Agreement (DPA) is a legal requirement under GDPR Article 28. The DPA establishes the terms under which the data processor handles personal data on your behalf, and your audit should verify compliance with these specific terms.
Learn about Data Processing AgreementsIf a processor fails an audit, you should document the findings and notify the processor of the deficiencies. Request a remediation plan with clear deadlines. If the processor cannot or will not address the issues, you may need to terminate the agreement and find an alternative processor. Continued use of a non-compliant processor puts your own GDPR compliance at risk.
Yes, GDPR Articles 40 and 42 allow you to rely on approved codes of conduct and certifications as evidence of compliance. However, you should verify that the certification covers all the requirements in your Data Processing Agreement. If gaps exist, you should request additional documentation from the processor.
A risk assessment evaluates the level of risk associated with each data processor based on factors such as the volume of personal data processed, whether sensitive or confidential data is involved, and whether processing activities are intrusive to data subjects. The risk level determines which audit method is most appropriate.
You can automate audits using vendor management software that helps you track risk assessments, manage audit templates, send and receive audit requests, handle reminders automatically, and structure follow-ups. This is especially valuable when managing multiple data processors with different risk levels and audit requirements.
GDPR requires you to document all audit activities, including risk assessments of each data processor, audit results, communications with processors about the audits, follow-up actions taken, and the processors' overall compliance status. This documentation demonstrates your accountability as a data controller.
Learn more about managing your data processors, creating Data Processing Agreements, and ensuring GDPR compliance across your supply chain.














.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.