Information Security Management › ISAE
Becoming Compliant: .legal's ISAE 3000 & ISAE 3402

Information security is more important today than ever before. Handling data in a secure, proportional, and transparent manner has become a crucial part of modern business operations, and for some companies, obtaining ISO 27001 certification is the natural choice.
ISO 27001 sets requirements for establishing, implementing, maintaining, and continuously improving an information security management system (ISMS). By meeting the requirements of ISO 27001 and getting certified, a company shows its high level of dedication to safeguarding personal data. This involves establishing a reliable and efficient ISMS that prioritises information security, handles risks effectively, and enhances the information security performance continually.
This not only ensures data processing security for data subjects and other stakeholders but also fosters a work culture that values security and resistance to threats.
ISO 27001 is an internationally recognised management standard for information security. Among other things, this standard establishes the criteria for risk management, process documentation (RoPA), and the assignment of roles and responsibilities concerning information security. Therefore, the standard serves as a management tool that helps companies protect data, including personal information, in a secure and trustworthy manner.
The goal of the ISO standard is to enable efficient information security management that suits your company's particular requirements and needs. Additionally, it maintains the consistency of effectiveness in every stage, which is why the ISO standard also ensures ongoing enhancement.
What is an Information Security Management System (ISMS)?
Getting an ISO 27001 certification is a way of showing that your company follows the standard's requirements and cares about information security – both before, during, and after certification. Ultimately, this strengthens customer trust and ensures compliance with legal requirements for data and privacy protection.
Now - what are the steps to begin the ISO 27001 certification process? The ISO 27001 standard contains different requirements and guidelines, and these can for instance be accessed through .legal’s ISMS product or bought from Dansk Standard (more on that subject later).
However, there are some key topics that need to be addressed in order to obtain certification. The following is a list of basic steps to set up an ISMS with a focus on the ISO 27001 requirements:
If you are considering automation, see: Do You Really Need GDPR Compliance Software? Here’s How to Know
... and if you do, see our overview of GDPR, Information and Cyber Compliance Software Tools
Becoming ISO-certified is a process that involves more than just obtaining the certification. It includes a comprehensive approach to information security and the standards set for risk management, resilience against threats, and the general maintenance of high functionality. This must also be documented and proven to show that they have become an integrated part of the company's daily operations.
Once the company has followed and applied the previous steps, an audit is carried out by a certification body. This audit must verify that the company has met the standards of ISO 27001. If this is proven, the company will obtain an ISO certification.
Thus, it is not enough to rely on an external company for auditing; it is crucial to secure high commitment from both management and employees, as well as a systematic method with the required resources at hand.
By following the ISO requirements and getting certified, the company shows that it has a high level of information security, which also means better protection of data and systems. This benefits the company's employees, customers, and other stakeholders.
Hence, it takes more than just casual involvement to fulfill the ISO standards — both from leaders and staff. We have gathered some helpful tips for a smooth implementation based on best practices, so your company can reach ISO 27001 compliance:
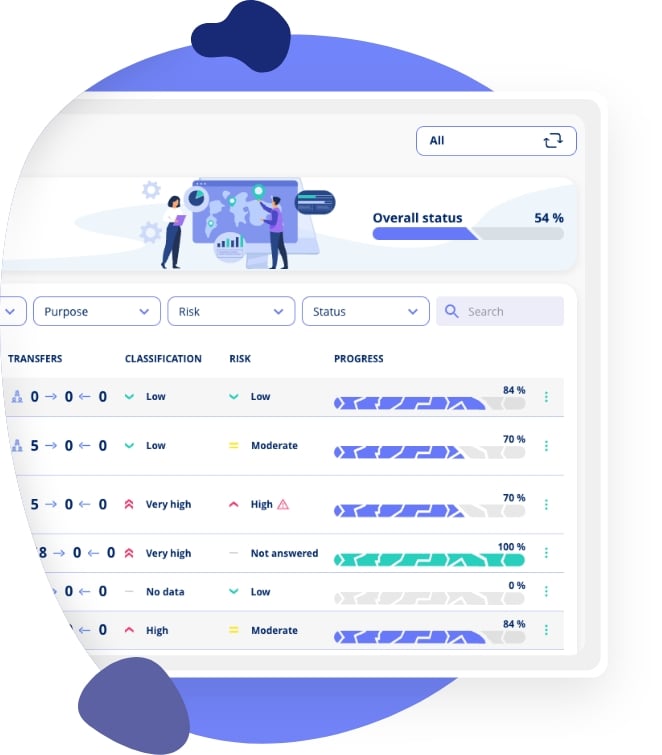
ISO certification can help your company in many ways, especially with data and information security. To ease the process of implementing and maintaining ISO in your company, .legal has developed a secure and easy-to-use ISMS in order to meet ISO requirements.
.legal's ISMS for IT-security & NIS2 compliance
This ISMS includes a CIA-friendly framework for risk assessments, control implementation, ongoing auditing, and improvement. The framework can also be adjusted to fit your company's specific needs and rules. This makes data protection and risk reduction easy and convenient without compromising the level of security.
It is fundamentally required to have an information security policy. There should also be appropriate policies related to specific topics, such as an access control policy or a password policy. The specific policies a company needs can vary depending on the nature and requirements of the business.
Annex A provides a list of potential information security controls. Companies can choose from the provided controls based on their situation; not every control may be relevant to them. The measures in Annex A are not obligatory by themselves, but it is recommended to review and adopt them if essential for the organisation's security needs.
ISO 27001 requires risk assessment reports and documented processes for managing risks. There may be other documents needed as well, depending on the company in question.
Learn more: ISO 27001 Compliance GuideMost companies do not need ISO 27001 certification, but it offers benefits including: (1) providing a guide for implementing relevant information security measures, (2) demonstrating compliance with international standards, (3) enhancing the company's reputation, and (4) strengthening overall security posture. It's particularly relevant for IT companies, financial institutions, and healthcare sectors handling sensitive data.
Stay on top of compliance: .legal's Frameworks solutionISO 27001 certification typically takes 6-12 months for smaller organisations and 12-24 months for larger enterprises. The timeline depends on your organisation's size, current security maturity, resource allocation, and complexity of operations. Using automated ISMS platforms like .legal can significantly reduce implementation time.
ISO 27001 is the certifiable standard that defines requirements for an ISMS. ISO 27002 is a code of practice providing guidance on information security controls. ISO 27001 tells you WHAT you must do, whilst ISO 27002 explains HOW to implement the controls.
Main ISO 27001 compliance requirements include: establishing an ISMS scope, conducting risk assessments, implementing security controls, creating information security policies, assigning roles and responsibilities, maintaining documentation, performing internal audits, conducting management reviews, and undergoing external certification audits. The standard also requires continuous improvement and monitoring.
Explore requirements in detail: ISO 27001 Compliance RequirementsISO 27001 certification costs vary based on organisation size and complexity. Typical expenses include consultant fees, ISMS software, employee training, internal audit costs, and external certification audit fees. Small organisations might spend £10,000-30,000, whilst larger enterprises can spend £50,000-200,000+. Compliance platforms like .legal reduce costs through automation and efficiency.
Yes, ISO 27001 certification is valid for 3 years. During this period, organisations must undergo annual surveillance audits to demonstrate continued compliance. After 3 years, a full recertification audit is required to renew the certification.
Annex A contains 93 security controls across 4 categories, serving as a comprehensive checklist for information security measures. Organisations select relevant controls based on their risk assessment and document why certain controls are or aren't applicable. This ensures a tailored approach whilst maintaining alignment with ISO 27001 requirements.
Discover our guides on ISO 27001 implementation, compliance checklists, and how to build an effective ISMS for your organisation.
















.jpeg)

.jpg)
.jpg)



.jpg)

-1.png)



.jpeg)








.jpg)





Info
.legal A/S
hello@dotlegal.com
+45 7027 0127
VAT-no: DK40888888
Support
support@dotlegal.com
+45 7027 0127
Need help?
Let me help you get started

.legal is not a law firm and is therefore not under the supervision of the Bar Council.